Features
Automated Asset Discovery Without Active Scanning
Attack surface management isn't just about the assets you know, it's about uncovering the ones you don't. Automated Discovery runs continuously in the background to identify assets, subdomains, and external threats associated with your organisation, without touching your infrastructure.
Discover Assets Unknown to You
Attack Surface Center's automated discovery capabilities passively identify your organisation's assets across your external attack surface without sending traffic to your infrastructure. Our automated reconnaissance discovers subdomains, IP addresses, web applications, and forgotten infrastructure that could expose your organisation to cyber threats.
Unlike active vulnerability scanning, which sends traffic to your systems, the automated discovery tools use passive techniques that include certificate transparency log analysis, DNS intelligence, OSINT data sources, and curated subdomain wordlists to map your attack surface without touching your infrastructure. This non-invasive approach discovers assets continuously without operational impact, scan notifications, or potential service disruptions.
Automated discovery runs continuously in the background, identifying new assets as they're exposed and detecting shadow IT resources created outside your normal IT processes. From newly deployed cloud instances to forgotten development subdomains, our passive reconnaissance provides comprehensive visibility into your expanding attack surface.
Surface what you don't know you're missing
Shadow IT, forgotten cloud resources, and legacy infrastructure are among the most common sources of serious breaches. Automated Discovery helps you find these before attackers do, without requiring manual effort or active probing of your systems.
Fully passive
All automated discovery tools work from public intelligence sources only. No traffic is directed at your assets, so there's zero operational impact.
Always running
Once configured, discovery runs automatically on a recurring basis. There's no scheduling required, as findings appear when they're identified.
Directly actionable
Discovered assets are automatically created or updated in your inventory, appear on the Attack Surface Map, and are available for scanning immediately.
No manual work
Verification of your root domains is a one-time step. After that, discovery maintains your inventory without any ongoing intervention.
Discover Subdomains You Didn't Know Existed
Over time, organisations accumulate subdomains from old projects, third-party services, and development environments - many of which are forgotten but remain publicly accessible. Automated subdomain enumeration surfaces these systematically, keeping your inventory complete.
- Intelligence-led enumeration: We combine curated subdomain wordlists with intelligence-led techniques to maximise coverage across your domain's namespace.
- Certificate Transparency monitoring: Public certificate issuance logs reveal subdomains the moment new TLS certificates are issued, and are often the earliest available signal of new deployments or shadow IT.
- Automatic asset creation: Newly discovered subdomains are automatically added to your asset inventory and reflected in the Attack Surface Map, ready for scanning or manual review.
- DNS record enrichment: Discovered assets are enriched with DNS records (A, CNAME, MX, TXT) to provide immediate context about what's running and where it points.
Automatically Detect Email Security Misconfigurations
Weak or missing email authentication records are a leading enabler of phishing and domain spoofing attacks. Automated discovery continuously checks your domains for SPF, DMARC, DKIM, and MTA-STS configurations, surfacing gaps before attackers can exploit them.
- SPF record analysis: Automatically retrieve and evaluate SPF records for each of your domains, identifying missing records, overly permissive configurations, and syntax errors that could allow spoofing.
- DMARC policy assessment: Check for the presence and enforcement level of DMARC policies across your domains. Weak or missing DMARC records leave your brand open to impersonation and phishing.
- DKIM key discovery: Probe for published DKIM selector records to confirm signing keys are in place. Missing or misconfigured DKIM records undermine email authentication even when SPF and DMARC are present.
- MTA-STS enforcement checks: Verify whether MTA-STS policies are published and correctly configured for your domains, ensuring inbound mail transport is protected against downgrade and interception attacks.
Detect Typosquatting and Phishing Domains Targeting Your Brand
Attackers frequently register domains that look like yours through misspellings, homoglyphs, and hyphenated variants, to conduct phishing campaigns against your customers and staff. Our typosquatting detection tools monitor for these registrations and surface them as potential threats.
- Lookalike domain monitoring: Continuously search for registered domains that could be used to impersonate your organisation, including misspellings and character substitutions.
- Homoglyph detection: Identify domains that use visually similar characters (e.g. rn vs m, 0 vs o) that are easily missed by users but trivial for attackers to register.
- Hyphenated and variant detection: Surface hyphenated versions and common structural variants of your domains that could serve as convincing phishing endpoints.
- Collaborative investigation: Findings are created as vulnerabilities in your inventory. Your team can investigate, assess the threat level, and coordinate blocking at the edge.
IP Address and Email Discovery
Beyond domain and subdomain discovery, automated tools surface the IP addresses and email addresses associated with your organisation to give you a more complete picture of your external footprint and potential social engineering exposure.
- Passive IP enumeration: Identify IP addresses associated with your domains through DNS resolution, WHOIS data, and other passive intelligence sources without scanning those addresses directly.
- Email address discovery: Surface email addresses associated with your domains from public sources. Useful for understanding your phishing exposure and social engineering risk.
- Email security posture: Automatically check for the presence of SPF, DKIM, and DMARC records on your domains to identify gaps in your email security configuration.
- WHOIS enrichment: Retrieve registration details for discovered domains and IP ranges, providing additional context about ownership and hosting relationships.
How Automated Discovery Works
Attack Surface Center’s automated discovery operates entirely through passive reconnaissance, gathering intelligence about your attack surface without sending any traffic to your infrastructure.
Domain Verification
After you verify domain ownership, our automated discovery tools begin continuous monitoring. Verification ensures we only discover assets you’re authorised to enumerate.
Continuous Intelligence Gathering
Our systems continuously monitor certificate transparency logs, passive DNS databases, OSINT sources, and other intelligence feeds for information about your domains.
Asset Identification
Discovered subdomains, IP addresses, and infrastructure are automatically validated, classified, and enriched with contextual information about hosting providers, technologies, and security posture.
Automatic Inventory Updates
Valid assets automatically populate your asset management system with details including DNS records, IP addresses, hosting provider, identified technologies, and last discovery date.
Attack Surface Map Integration
Newly discovered assets are immediately reflected on the Attack Surface Map, giving you a visual representation of your evolving attack surface in real time.
No Infrastructure Impact
Automated discovery never sends traffic to your assets, eliminating concerns about scan-induced outages, rate limiting, security control triggers, or operational disruptions.
Identify assets and potential threats without lifting a finger
Sign up free. Automated discovery runs from your first verified domain with no configuration required.
Common questions
Once you’ve subscribed and verified your root domain names, the available automated discovery tools run regularly in the background without any scheduling or manual invocation required. Findings are automatically imported into your asset inventory.
No. All automated discovery tools use passive, intelligence-led techniques. They work from public data sources only and never send traffic directly to your assets. There is zero operational impact.
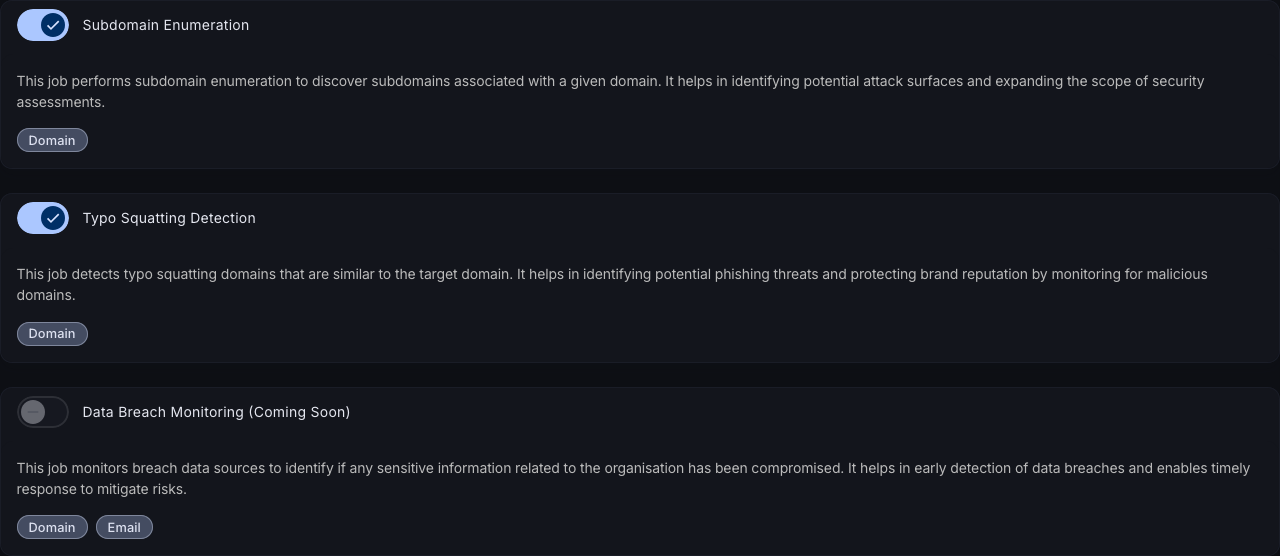
Yes. Users with the appropriate permissions can toggle individual discovery tools on or off at any time from the automations settings page.
Discovery runs automatically on a regular cadence based on your plan. Starter plans run automations monthly; Advanced plans run them daily for near-continuous coverage.
Yes, the team are actively working on expanding automated discovery to cover additional external and internal attack surface scenarios. Sign up and stay updated on future releases.