Features
Vulnerability Management Platform for Security Teams
Log, track, and prioritise vulnerabilities across your environment. Streamline remediation workflows and reduce your organisation's risk exposure with collaborative vulnerability management.
What is Vulnerability Management?
Vulnerability management is the continuous process of identifying, evaluating, prioritising, and remediating security vulnerabilities in your organisation’s IT infrastructure, applications, and systems.
Effective vulnerability management helps security teams:
Identify Security Weaknesses
Discover vulnerabilities across your attack surface through automated scanning, penetration testing, and security assessments before attackers can exploit them.
Prioritise Remediation Efforts
Assess the risk associated with each vulnerability to focus on the most critical issues that could have the greatest impact on your organisation.
Track Remediation Progress
Monitor the status of vulnerabilities over time, ensuring that they are addressed in a timely manner and that your security posture is continuously improving.
Reduce Risk Exposure
By systematically managing vulnerabilities, you can significantly reduce your organisation's risk exposure and protect against potential cyber threats.
Track and Prioritise Security Issues with Confidence
Security isn’t just about finding issues; it’s about managing them effectively. Our vulnerability management platform ensures that you have the tools to log, manage, and analyse vulnerabilities in real-time.
The workflows support collaboration across different teams, providing a clear path from vulnerability discovery to remediation. This helps you reduce your organisation’s risk exposure to maintain a strong security posture.
Discover
Passive reconnaissance surfaces assets, subdomains, and threats you didn't know existed.
Inventory
Every asset is catalogued, enriched with context, and reflected on your Attack Surface Map.
Scan
Port and web application scans probe your inventory for exposed services and vulnerabilities.
Prioritise
Severity, asset criticality, and attack chain context surface what to fix first.
Remediate
Assign tasks, track progress, and close findings - all without leaving the platform.
Key Vulnerability Management Features
The Attack Surface Center vulnerability management platform offers a range of features designed to streamline your security operations and enhance your ability to manage vulnerabilities effectively.
Risk Scoring
Understand the potential impact of each vulnerability with our risk scoring system, allowing you to focus on the most critical issues first.
Custom Reporting
Create custom assessment reports to share with stakeholders, providing insights into your security posture and remediation progress.
Import and Export
Easily import vulnerabilities from external sources or export them for reporting and compliance purposes.
Automated Scanning
Use our automated scanning capabilities to continuously monitor your environment for new vulnerabilities.
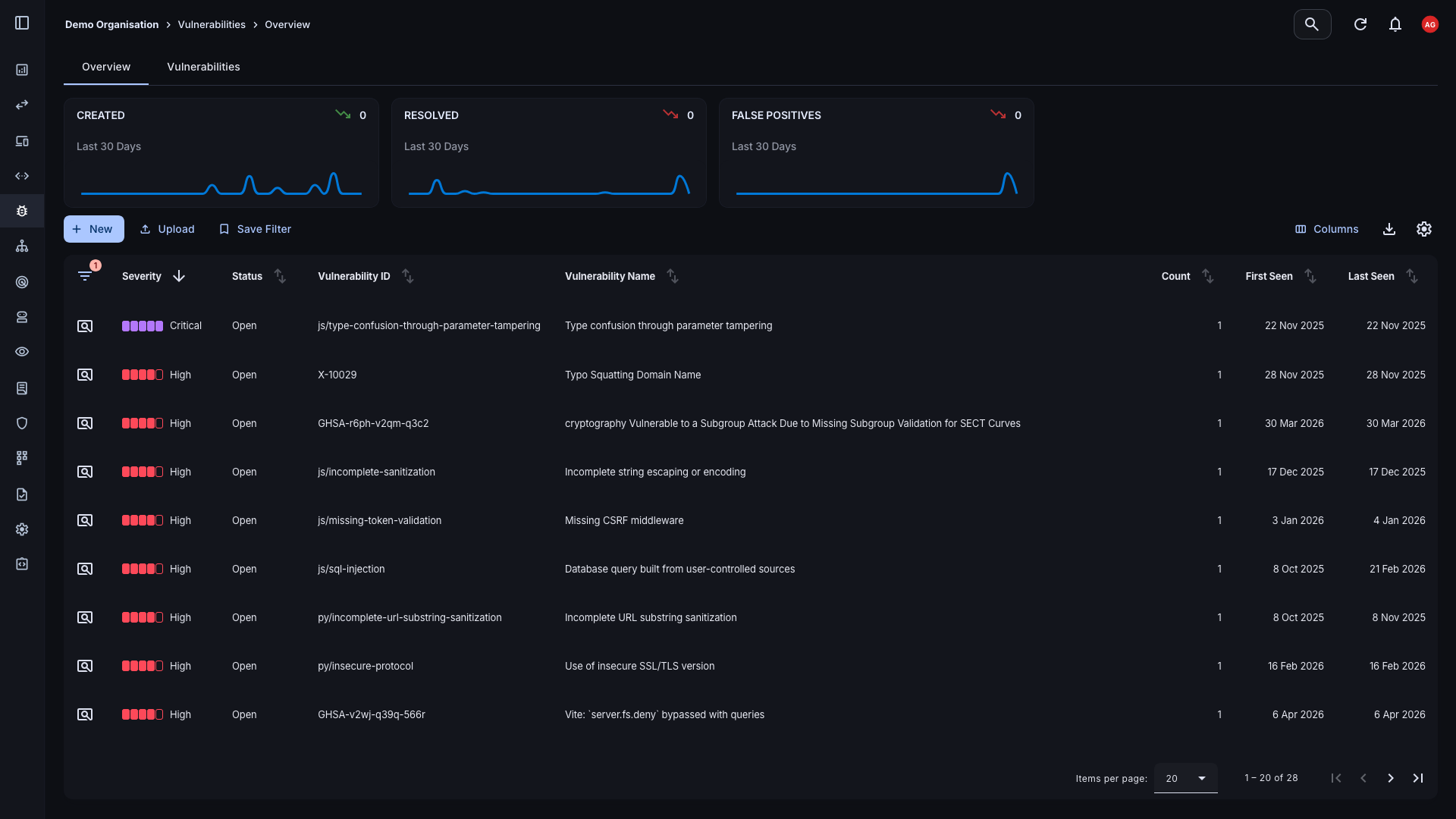
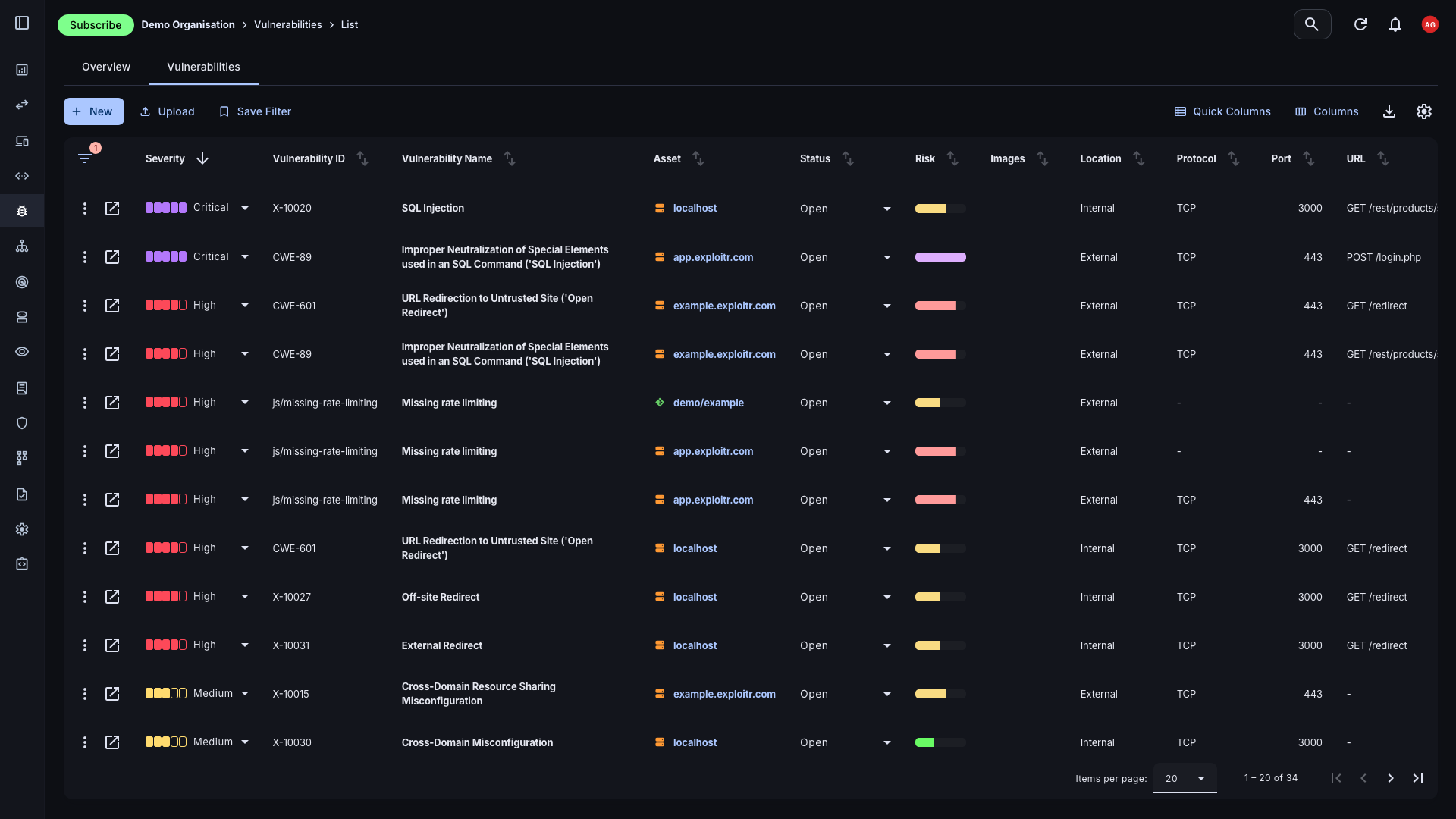
Detailed Security Vulnerability Tracking
Efficiently view vulnerabilities across your organisation within the vulnerability overview dashboard or vulnerability list view. The dashboard provides an overview of all vulnerabilities, allowing you to quickly filter and sort by severity, status, asset, and many more criteria.
- Vulnerability List View: Delve into individual vulnerabilities for detailed information about affected assets, severity, services, and URLs.
- Overview Dashboard: Get a high-level view of all vulnerabilities, with quick filtering and sorting capabilities.
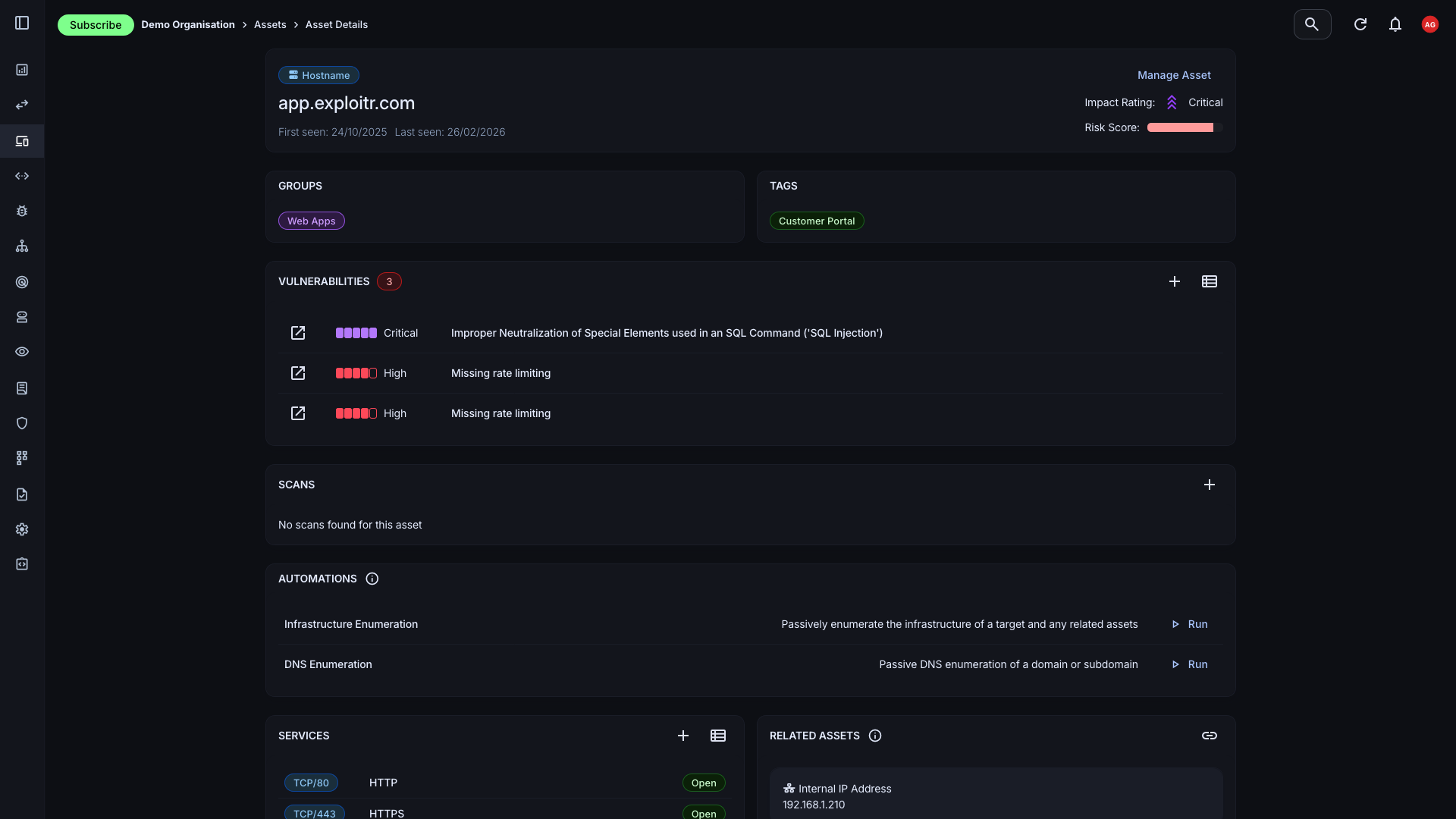
Seamless Integration with Asset Management
The Attack Surface Center's vulnerability management platform is tightly integrated with our asset management feature, allowing you to easily associate vulnerabilities with specific assets.
- Cloud Vulnerability Management: Manage vulnerabilities across your cloud infrastructure, including AWS, Azure, and Google Cloud Platform.
- Asset Association: Associate security vulnerabilities with assets, providing context and enabling targeted remediation efforts.
- Asset Context: View detailed information about each asset, including its risk score, associated vulnerabilities, and contextual information.
Remediation and Prioritisation
Manage the severity, status, and optionally provide comments on each vulnerability to facilitate collaboration and tracking over time.
- Collaboration: Work together in real-time with your team to resolve vulnerabilities, ensuring that everyone is on the same page.
- Status Management: Easily update the status of each vulnerability to keep your team aligned.
- Comment on Changes: Optionally include comments to help track the progress of remediation efforts and ensure vulnerabilities are addressed in a timely manner.
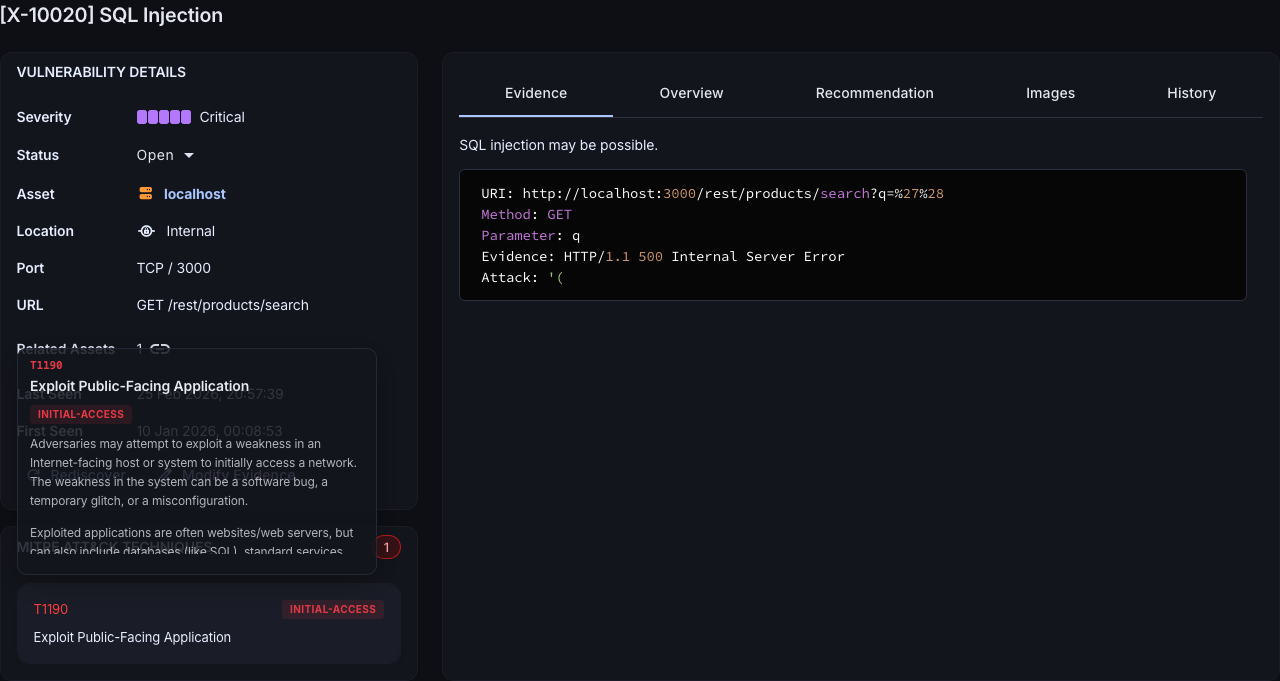
Risk Scoring and Contextual Information
The risk scoring system provides a clear understanding of the potential impact of each vulnerability. Focus on the most critical issues and understand the risk associated with each asset and vulnerability.
- Severity: The inherent risk of the vulnerability, ranging from Informational to Critical, based on industry standards such as CVSS.
- Impact: The potential impact on your organisation if the vulnerability were to be exploited.
- Normalised Risk Score: A simple, easy-to-understand risk score that helps you prioritise vulnerabilities effectively across your whole estate.
Take Charge of Your Vulnerability Management
The Attack Surface Center provides the tools you need to protect your organisation from cyber threats: asset discovery, risk management, and vulnerability scanning in one platform.
Common questions
Vulnerability management is an ongoing process of identifying, classifying, prioritising, and remediating security vulnerabilities across your organisation’s IT assets. Vulnerability management is a continuous discipline to ensure that new vulnerabilities are identified and managed as your environment changes over time.
Vulnerability scanning is the process of using automated tools to identify potential vulnerabilities in your systems and applications. Vulnerability management, on the other hand, encompasses the entire lifecycle of managing vulnerabilities, including identification, classification, prioritisation, and remediation. Vulnerability management is a broader discipline that includes vulnerability scanning as one of its components.
The Attack Surface Center provides a comprehensive vulnerability management platform that allows you to log, track, and prioritise vulnerabilities across your environment. With features like risk scoring, custom reporting, and seamless integration with asset management, our platform helps you streamline remediation workflows and reduce your organisation’s risk exposure.
Yes. If you already use third-party scanning tools, such as Nmap or ZAP, you can import their results directly into the Attack Surface Center and manage everything from a single platform. We’re always continuing to expand our features, so if there are tools that you use and we don’t currently support them – just let us know!
Each vulnerability is scored based on its severity, potential impact, and contextual factors specific to your environment. Scores are normalised to give you a simple, consistent way to prioritise risks – so your team always knows what to fix first, without needing to manually triage every finding.
Yes. The Attack Surface Center’s vulnerability management platform includes collaboration features that allow your team to work together in real-time to resolve vulnerabilities. You can update the status of each vulnerability, add comments, and keep everyone aligned on remediation efforts.