Features
Automated Vulnerability Scanning
Schedule port scans and web application vulnerability scans to run continuously across your assets. Results feed directly into your dashboard. No manual effort, no missed windows.
Continuous scanning, zero manual effort
Scheduled scanning means your asset inventory stays current with the latest exposure data. Create a scan job once, set the schedule, and let the platform handle the rest.
Port scanning
Discover open ports and services across your assets to identify potential attack vectors and unexpected exposure on your network perimeter.
Web application scanning
Scan your web applications and APIs for known vulnerabilities: misconfigurations, outdated components, injection points, and more.
Scheduled automation
Set scans to run weekly or monthly depending on your plan. Results are automatically imported into your vulnerability inventory.
Passive discovery
Supplement active scans with passive automated discovery. Gathering intelligence about your assets without sending any traffic to them.
Automated Vulnerability Scanning for Continuous Coverage
Attack Surface Center’s automated vulnerability scanning capabilities enable security teams to continuously monitor their infrastructure for security weaknesses, misconfigurations, and exposed services. Our integrated vulnerability scanning tools combine network port scanning and web application security testing to provide comprehensive coverage across your entire attack surface.
Schedule automated security scans to run continuously at intervals that match your security requirements – weekly, monthly, or annually. Discover open ports and exposed services on your network infrastructure, identify known vulnerabilities in web applications and websites, and maintain real-time visibility into your security posture without manual intervention.
Our vulnerability scanning engine integrates seamlessly with Attack Surface Center’s asset inventory and vulnerability management capabilities. Scan results automatically create or update vulnerability records in your centralised vulnerability management dashboard, enabling efficient prioritisation and remediation workflows.
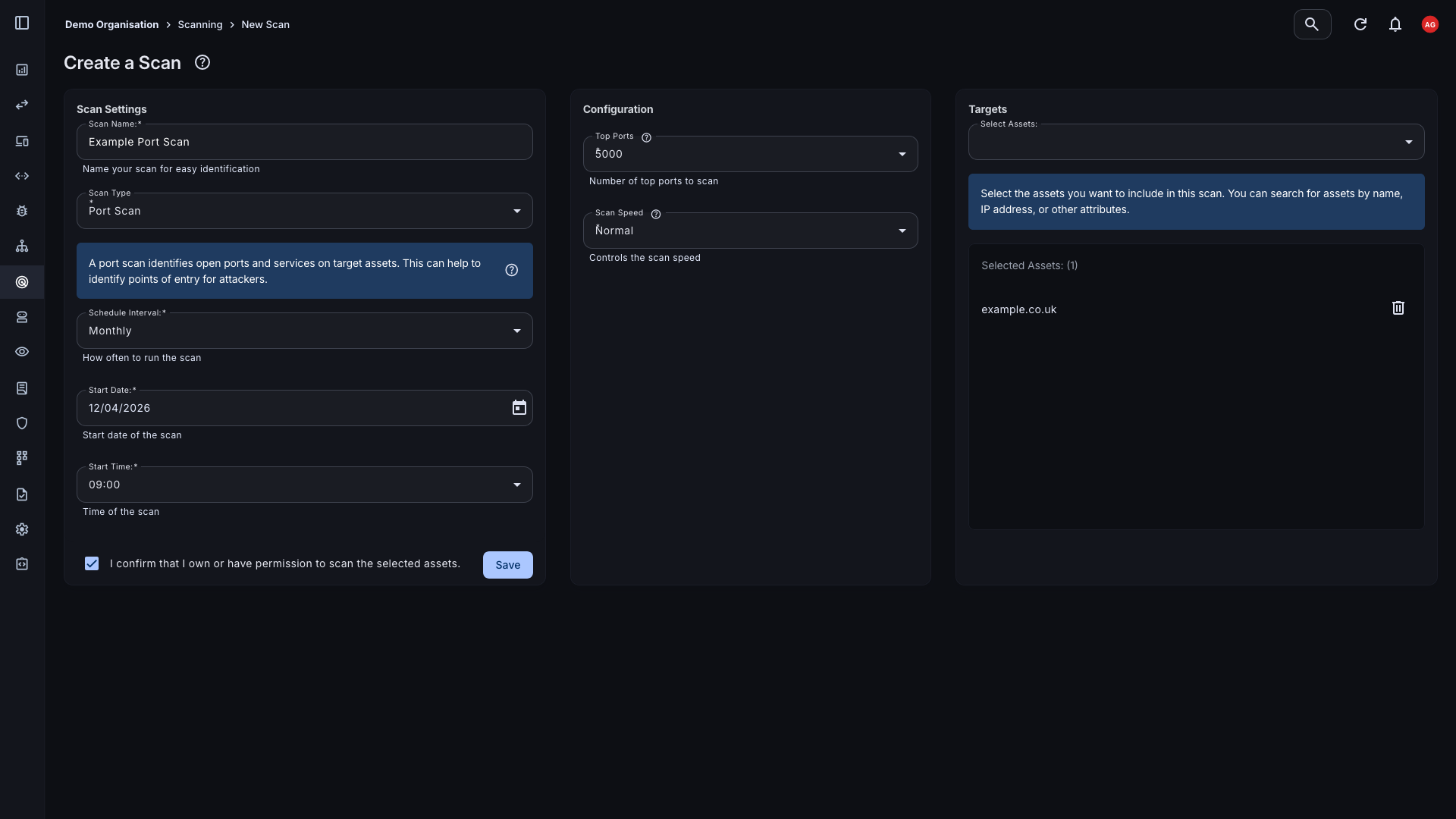
Network Port Scanning
Create port scanning jobs to discover open ports and services across your assets. Understanding what's listening on your network perimeter is a fundamental first step in managing your attack surface, and scheduled scans ensure that picture stays accurate over time.
- Flexible asset targeting: Target specific assets or asset groups within your inventory. Scans run against the assets you define, within your plan's scannable asset allowance.
- Scheduled and on-demand: Set a recurring schedule: monthly or weekly depending on your plan.
- Automatic result import: Open ports and services discovered during scanning are automatically added to your asset records and reflected in the Attack Surface Map.
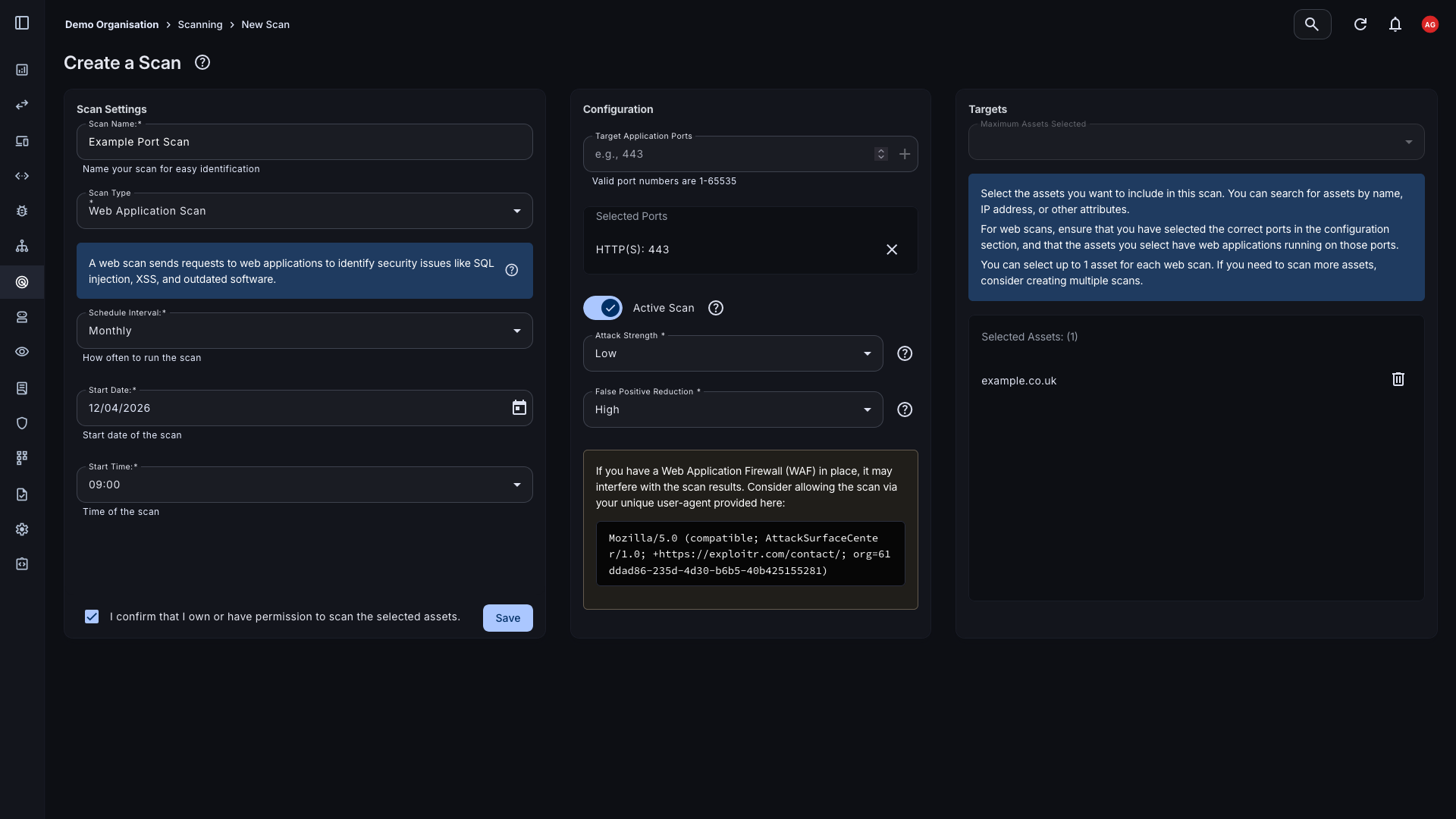
Web Application Vulnerability Scanning
Set up vulnerability scanning jobs to automatically scan your web applications and APIs for known weaknesses. Results are imported directly into your vulnerability management workflow, ready to triage and remediate.
- Known vulnerability detection: Scan for common web application vulnerabilities including injection flaws, authentication issues, outdated components, and security misconfigurations.
- API scanning: Extend scanning coverage to your APIs, not just your web-facing applications, to capture the full scope of your application attack surface.
- Results feed into remediation: Scan findings are automatically created as vulnerabilities in your inventory, with severity scores, asset association, and all the context you need to act.
From asset to finding in one pipeline
Every scan follows the same path — from your asset inventory through to actionable vulnerability records, with no manual steps in between.
Asset inventory
Scans run against assets already tracked in your inventory.
Scan job
Choose scan type, target assets, and set a schedule.
Automated scan
The platform runs the scan at the configured interval.
Results imported
Open ports and vulnerabilities appear in your dashboard automatically.
Remediation
Triage, assign, and track findings through to resolution.
Getting started in four steps
Once your assets are in the platform, continuous scanning takes minutes to configure.
Create a scan job
Select the assets you want to scan, choose the scan type (port or web application), and configure any relevant settings.
Set your schedule
Choose how frequently scans should run based on your plan. Weekly scans are available from Standard plans upward.
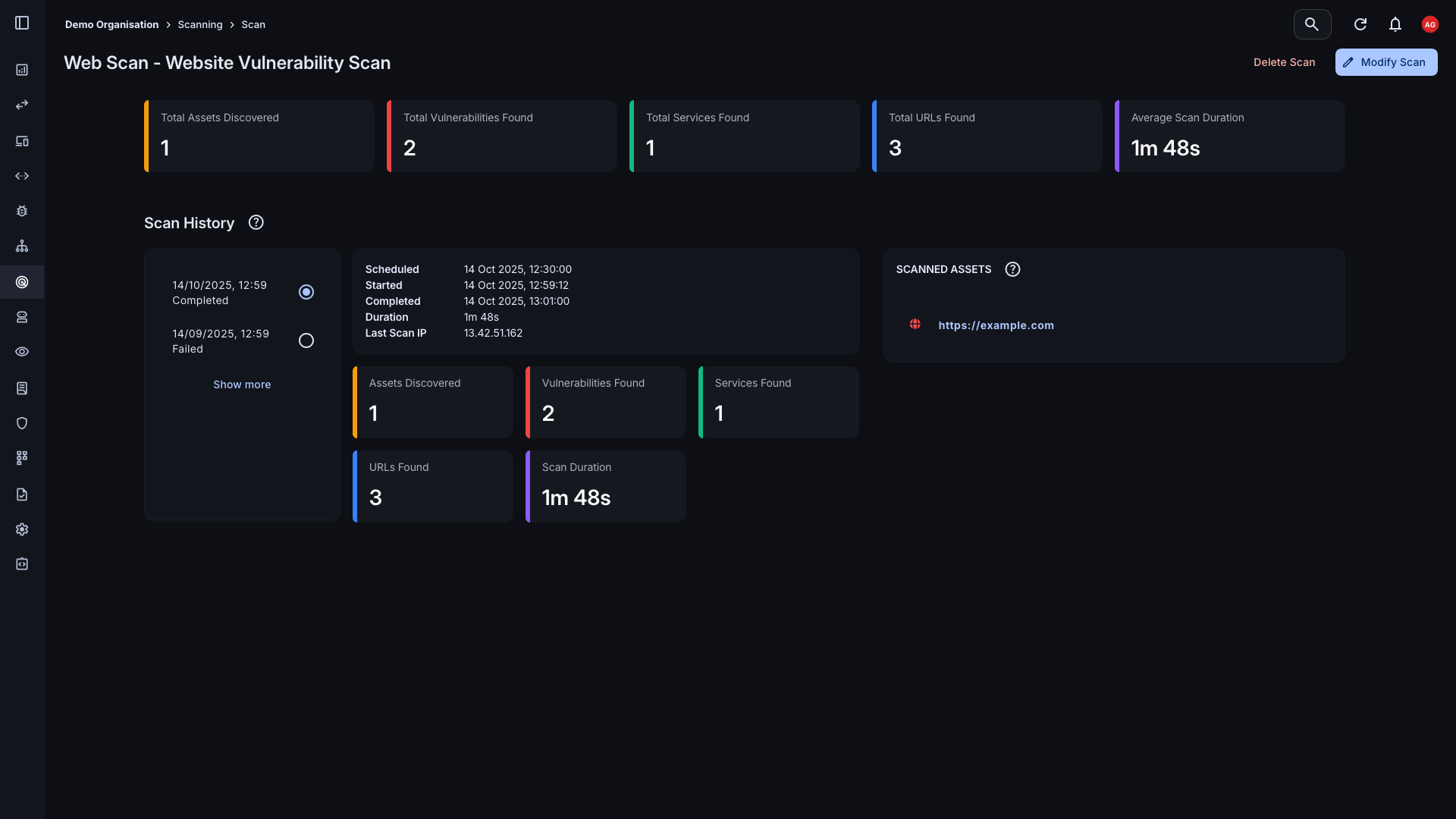
Review results
Once complete, scan results appear in your vulnerability dashboard. Filter by severity, asset, or scan date to prioritise your response.
Remediate and re-scan
Address findings in your workflow, then re-scan to confirm resolution. Continuous scheduling means emerging issues are caught in the next cycle.
Start scanning your attack surface
Sign up for free. Paid plans unlock scheduled scanning from your first billing month.
Common questions
The Attack Surface Center supports network port scanning and web application vulnerability scanning. Port scanning discovers open ports and services; web application scanning identifies known vulnerabilities in your applications and APIs.
Scan frequency depends on your plan. Starter plans support monthly scheduled scans; Standard plans support weekly scans.
Each plan includes a monthly allowance of scannable assets: domains, IP addresses, hostnames, URLs, and similar targets. Assets can be scanned as frequently as your schedule allows within the month. Additional assets can be purchased in-app if you need to expand coverage.
Port scanning identifies which ports are open and which services are running on your assets - useful for understanding network exposure. Vulnerability scanning actively tests your web applications and APIs for specific known weaknesses, such as CVEs, misconfigurations, and insecure components.
Yes. You can upload scan results from third-party tools such as Nmap and OWASP ZAP directly into the Attack Surface Center, centralising all your findings in one place.