Solutions
Attack Surface Management for CISOs
The CISO's job is to reduce risk and demonstrate that reduction clearly. Attack Surface Center gives you continuous visibility into your external risk posture, the data to prioritise your team's efforts, and the reporting tools to communicate security outcomes to the board and regulators.

What Attack Surface Center delivers for security leaders
CISOs need more than dashboards. They need a programme that continuously discovers risk, helps teams act on it, and produces evidence of progress. Attack Surface Center is built to support all three.
Continuous external visibility
Automated discovery runs around the clock to surface new assets, shadow IT, and external threats - giving you an always-current picture of what your organisation is exposing to the internet.
Risk-driven prioritisation
Vulnerabilities and assets are scored by risk, not just severity. Your team always has a data-driven basis for where to focus, reducing time wasted on low-impact findings.
Board-ready reporting
AI-assisted report generation and PDF exports help you communicate security posture and remediation progress clearly to senior stakeholders without manual effort.
Programme structure
Asset management, vulnerability tracking, risk register, and task management sit in a single platform, giving your security programme a consistent operating structure rather than a collection of disconnected tools.
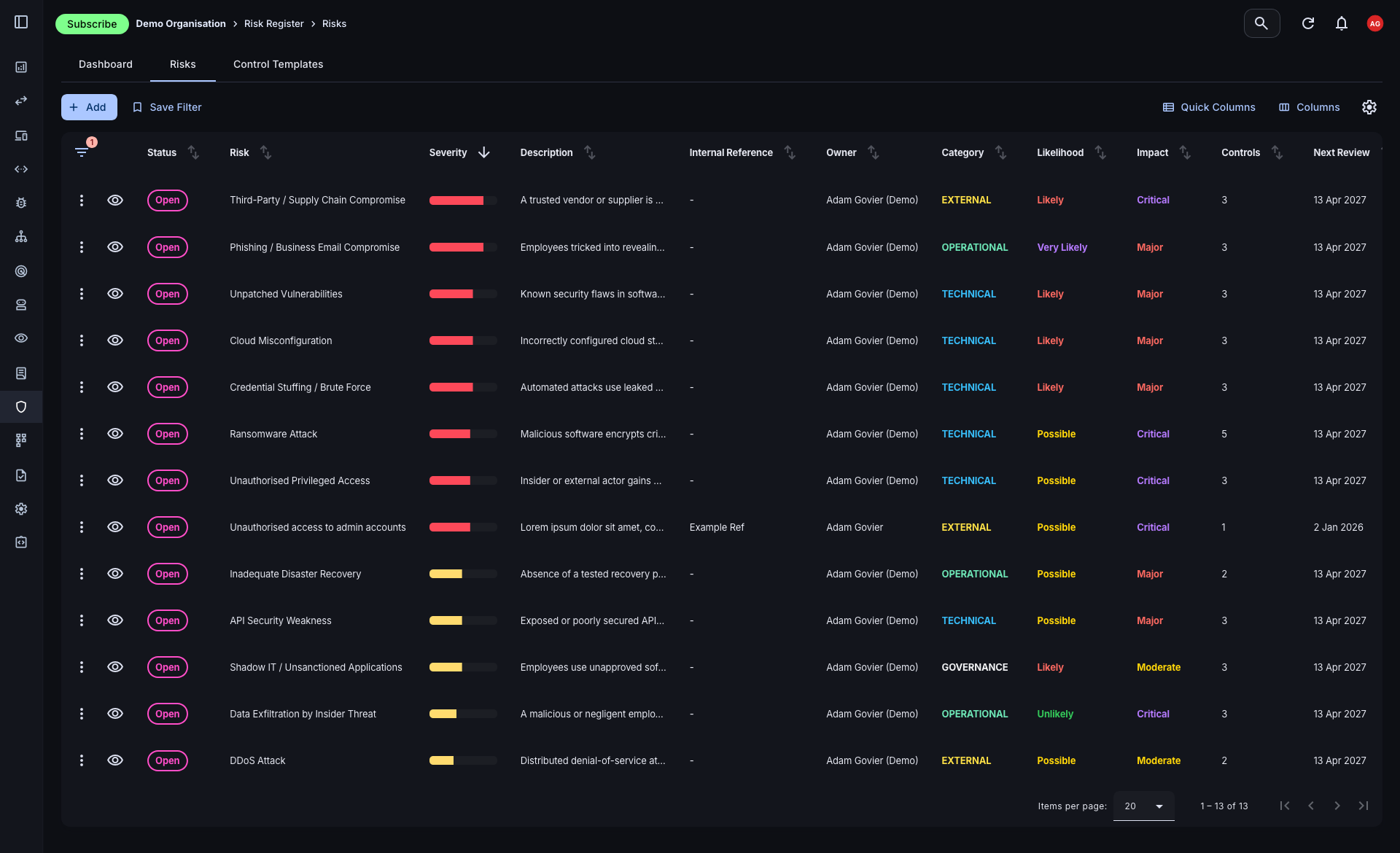
Connect technical findings to business risk
Vulnerability scores tell you what's broken. A risk register tells you what it means for the business. The Attack Surface Center brings both together, allowing you to maintain a structured risk register that sits alongside your asset and vulnerability data - in one platform, not a separate spreadsheet.
- Structured risk records: Document, assess, and track organisational risks with impact and likelihood ratings, assigned owners, and linked controls.
- Asset and vulnerability linking: Connect each risk record directly to the assets and vulnerabilities that underpin it, giving every entry its full technical context.
- Compliance alignment: A documented, maintained risk register supports frameworks including ISO 27001, SOC 2, Cyber Essentials Plus, and NIS2.
Communicate security posture clearly
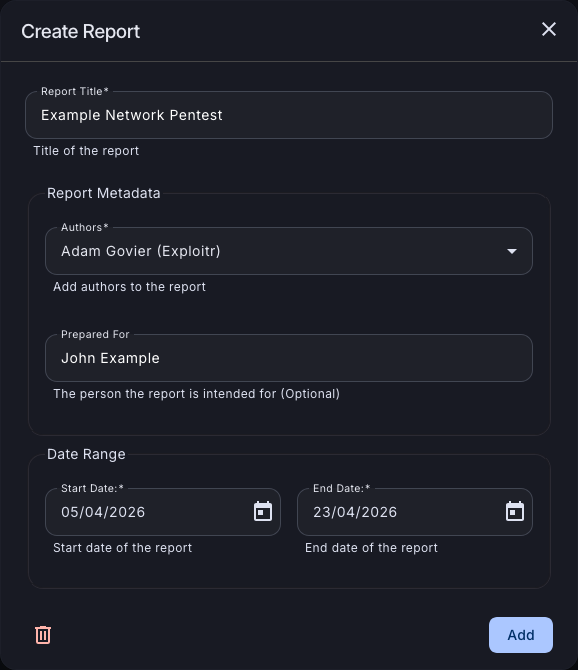
Manual reporting consumes time your team doesn't have. The platform's AI-assisted report generation produces clear, customisable security reports from your live data - suitable for board briefings, stakeholder updates, and compliance submissions.
- AI-powered generation: Generate written commentary and executive summaries from your vulnerability and risk data, with AI assistance to produce polished output quickly.
- PDF export: Export reports as PDFs for board packs, audit submissions, or stakeholder distribution - all from within the platform.
- Customisable structure: Tailor report content and scope to your audience, whether that's a technical team briefing, an executive risk summary, or an auditor's evidence pack.
The outcomes CISOs care about
From reducing your organisation’s attack surface to demonstrating that reduction clearly, the platform is built to support the outcomes that matter to security leadership.
Reduced attack surface
Automated discovery, continuous scanning, and structured remediation workflows shrink your exposure systematically over time.
Risk visibility
A unified view of assets, vulnerabilities, and risks gives you the context to make confident decisions about where to invest your team's effort.
Compliance evidence
Continuous monitoring, a maintained risk register, and exportable reports provide the evidence regulators and auditors expect.
Programme efficiency
Consolidating your security tooling into a single platform reduces overhead, removes duplication, and helps your team work faster with less context-switching.
Lead a more proactive security programme
Sign up free. Get full visibility of your external attack surface and start reducing risk from day one.
Common questions
The platform includes AI-assisted report generation that produces written summaries of your security posture, vulnerability status, and remediation progress from live data. Reports can be exported as PDFs suitable for board packs and stakeholder briefings, without requiring significant manual effort from your team.
Yes. The risk register, continuous monitoring, and exportable reporting support common security and compliance frameworks including ISO 27001, SOC 2, Cyber Essentials Plus, and NIS2. The platform provides the documentation, evidence, and structure that auditors typically expect.
Risk records can be linked directly to specific assets and vulnerabilities within the platform, so each risk entry carries its full technical context alongside the business-level impact and likelihood assessment. This removes the disconnect between your technical findings and your risk management process.
Seat limits vary by plan. See the pricing page for a full breakdown, or contact us if you need a custom arrangement for a larger team.
There is no implementation project. You sign up, verify your root domains, and discovery starts automatically. Your team can begin scanning assets and logging vulnerabilities the same day. Most organisations have a meaningful picture of their attack surface within the first 24 hours.