Solutions
Attack Surface Management for Compliance & Risk Teams
Compliance frameworks and risk management obligations require evidence of continuous monitoring, documented risks, and structured remediation. Attack Surface Center provides the inventory, risk register, and reporting tools to meet those obligations without building a separate compliance programme on top of your security operations.
Structured compliance and risk management, built into your security programme
Treating compliance as a separate workstream from security operations creates duplication and gaps. Attack Surface Center integrates your risk register, asset inventory, and vulnerability management into one platform so compliance evidence is a natural output of your day-to-day security work.
Continuous monitoring
Automated discovery and recurring scanning demonstrate the ongoing monitoring that frameworks like ISO 27001, NIS2, and SOC 2 require - without manual effort.
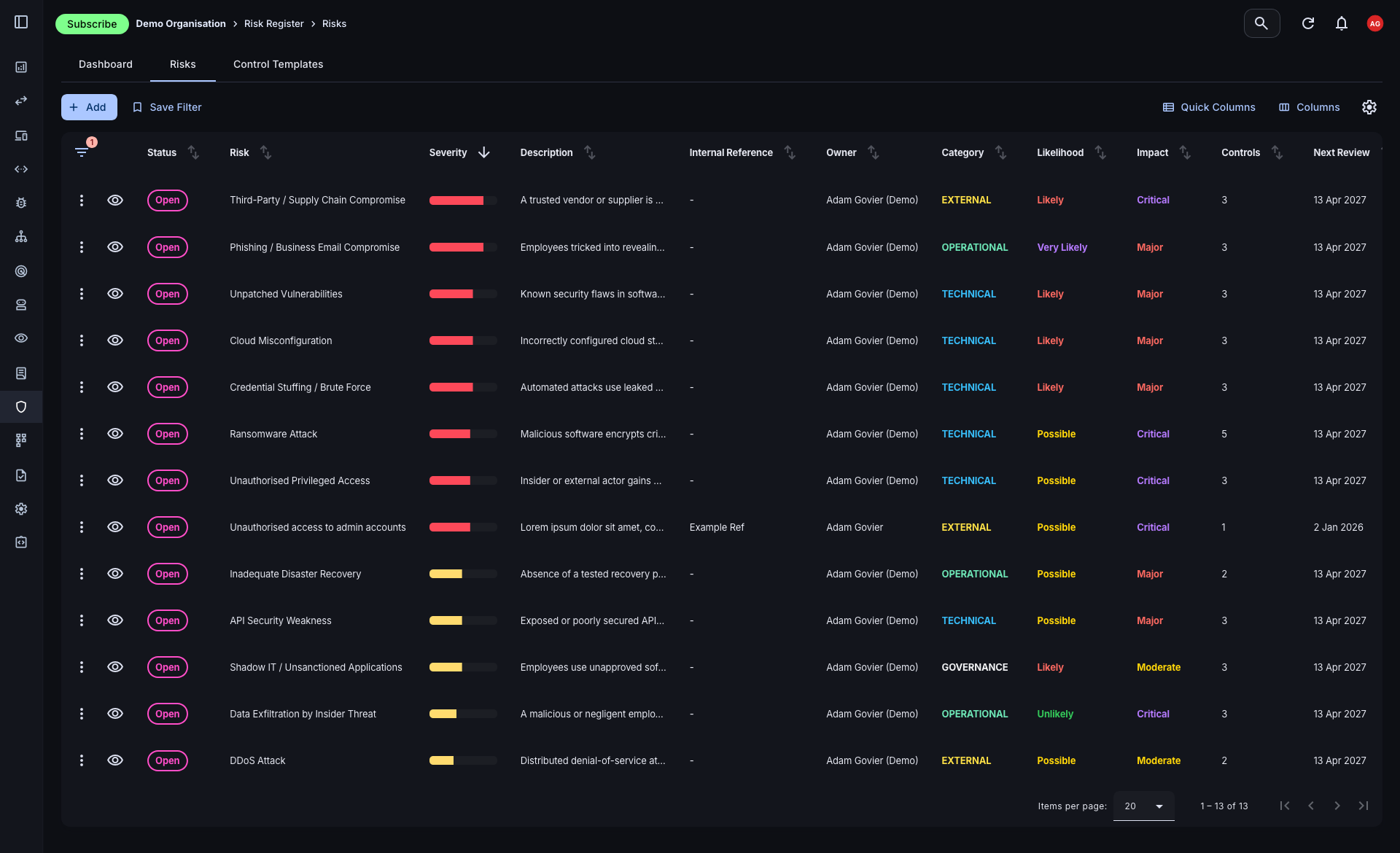
Structured risk register
Document, assess, and track organisational risks with a formal risk register that supports compliance audits and internal governance processes.
Audit-ready evidence
Exportable reports, risk records, and vulnerability history provide the documented evidence auditors and certifying bodies expect.
Integrated with technical findings
Risk records link directly to assets and vulnerabilities, so your compliance posture is grounded in real technical evidence rather than self-assessment alone.
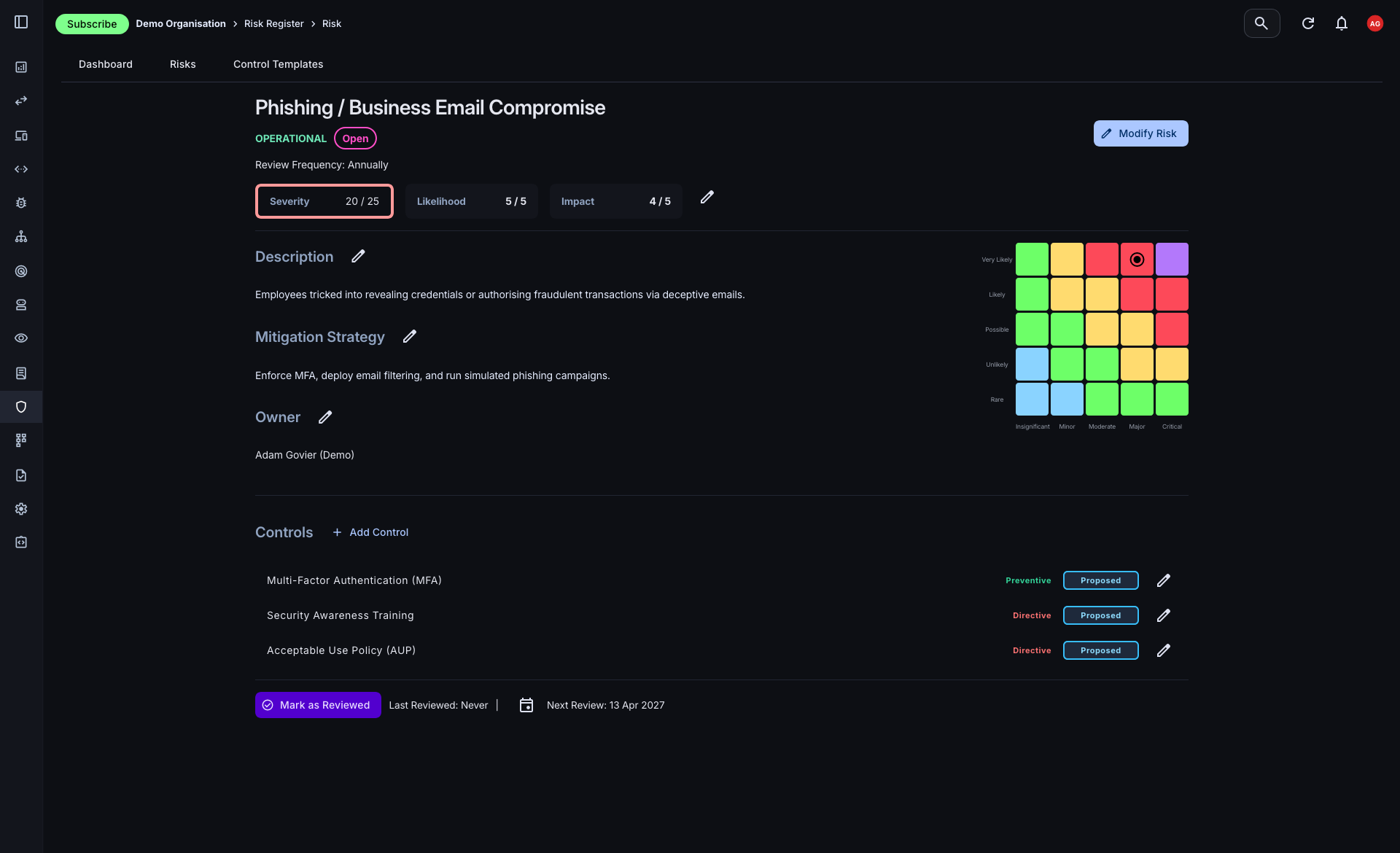
A structured risk register linked to your attack surface
Most risk registers live in spreadsheets disconnected from the underlying technical data. The Attack Surface Center risk register sits alongside your asset and vulnerability management, so every risk record can be linked to the specific assets and findings that substantiate it.
- Full risk lifecycle: Track risks from identification through assessment, mitigation, and review. Each record carries its impact rating, likelihood score, owner, and linked controls.
- Customisable controls: Build a reusable library of controls - preventive, detective, directive, or corrective - that can be applied across multiple risk records.
- Risk categorisation: Organise risks by category to reflect your risk taxonomy and make reporting by domain or business area straightforward.
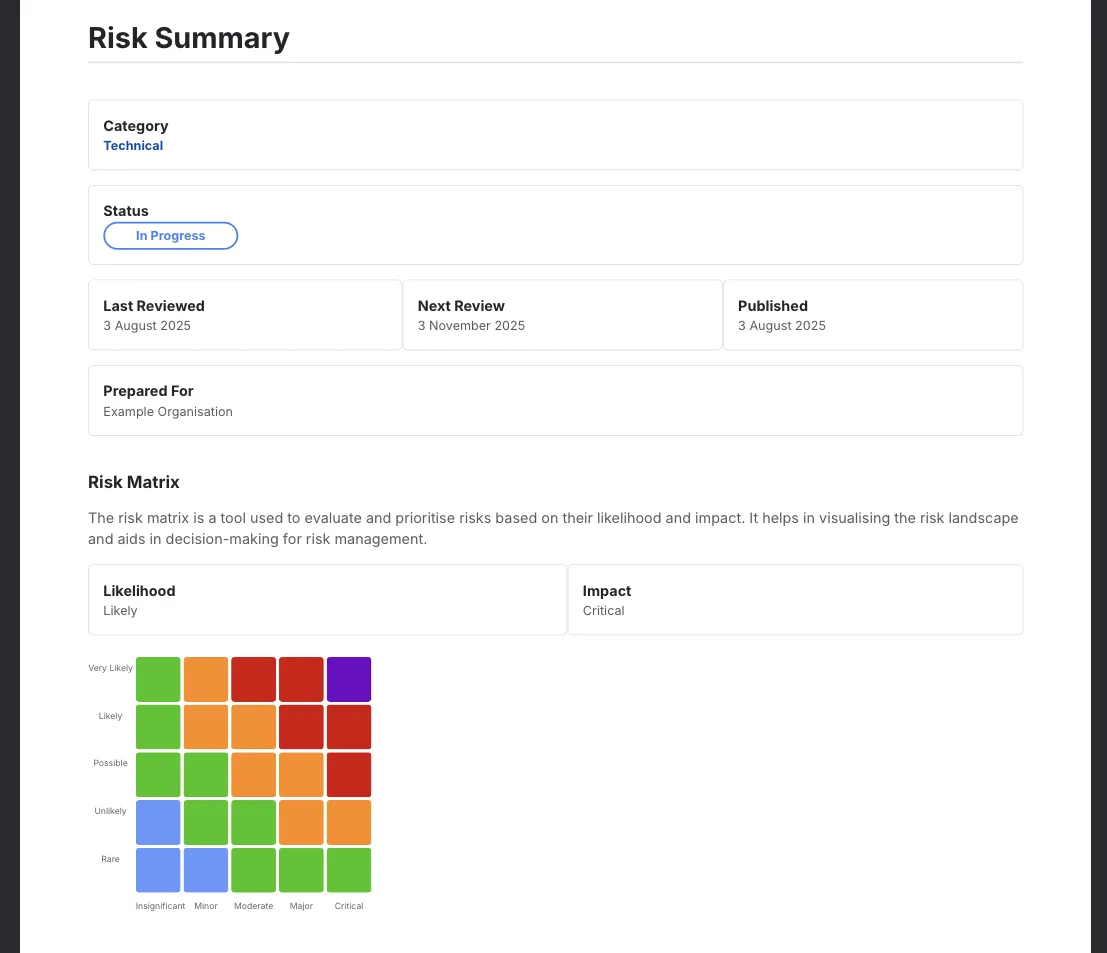
Produce audit-ready reports without manual effort
Pulling together evidence for an audit or board submission is one of the most time-consuming parts of a compliance function. The platform's reporting tools generate structured, exportable reports from your live data, covering vulnerability status, risk register summaries, and security posture assessments.
- AI-assisted report generation: Generate written commentary and executive summaries from your vulnerability and risk data using AI assistance, reducing manual drafting significantly.
- PDF export: Export reports in PDF format suitable for auditors, certifying bodies, board packs, or client-facing compliance submissions.
- Assessment and penetration test reports: Log findings from external assessments and generate structured reports that document scope, findings, and remediation status - all within the platform.
Framework alignment
Attack Surface Center’s continuous monitoring, risk register, and reporting capabilities support the requirements of common security and compliance frameworks.
ISO 27001
Continuous asset inventory, risk register, vulnerability management, and documented controls support the operational requirements of ISO 27001 certification.
SOC 2
Continuous monitoring, access controls, and documented risk management processes provide evidence for SOC 2 Type I and Type II audits.
Cyber Essentials Plus
Asset inventory, patch status visibility, and vulnerability scanning support the technical verification requirements of Cyber Essentials Plus.
NIS2
Continuous network monitoring, asset management, and vulnerability disclosure processes align with NIS2's operational security obligations for essential and important entities.
Build compliance evidence into your security programme
Sign up free. Start building a risk register and asset inventory that produces audit-ready evidence as a natural part of your security operations.
Common questions
The platform’s continuous monitoring, risk register, vulnerability management, and reporting capabilities align with the operational requirements of ISO 27001, SOC 2, Cyber Essentials Plus, NIS2, and similar frameworks. It does not provide certification itself, but supplies the processes, evidence, and documentation that support your compliance programme.
The risk register provides a structured, auditable log of every identified risk, including impact and likelihood assessments, assigned owners, linked controls, and current status. This gives auditors the documented evidence of a functioning risk management process that frameworks like ISO 27001 require.
Yes. Risk reports and vulnerability assessments can be exported as PDFs directly from the platform, suitable for sharing with auditors, certifying bodies, or including in compliance submissions.
Many frameworks require organisations to demonstrate that security monitoring is ongoing rather than point-in-time. Automated discovery and scheduled scanning in Attack Surface Center provide the continuous monitoring capability - and the evidence of it - that these frameworks expect.
Yes. The platform includes penetration test report management, allowing you to log findings from external assessments, generate structured reports, and track remediation of identified vulnerabilities - all within the same platform as your ongoing vulnerability management.