Solutions
Attack Surface Management for IT & Infrastructure Teams
IT and infrastructure teams are responsible for the systems that face the internet - but the full scope of what's exposed often isn't clear until something goes wrong. Attack Surface Center gives you a continuously updated inventory of every external-facing asset, the services running on them, and the vulnerabilities you need to address.
Complete visibility over your external-facing infrastructure
Infrastructure environments grow faster than inventories can keep pace with. Cloud deployments, contractor-created resources, and legacy systems accumulate over time, creating blind spots that are disproportionately likely to be exploited. Attack Surface Center closes that gap.
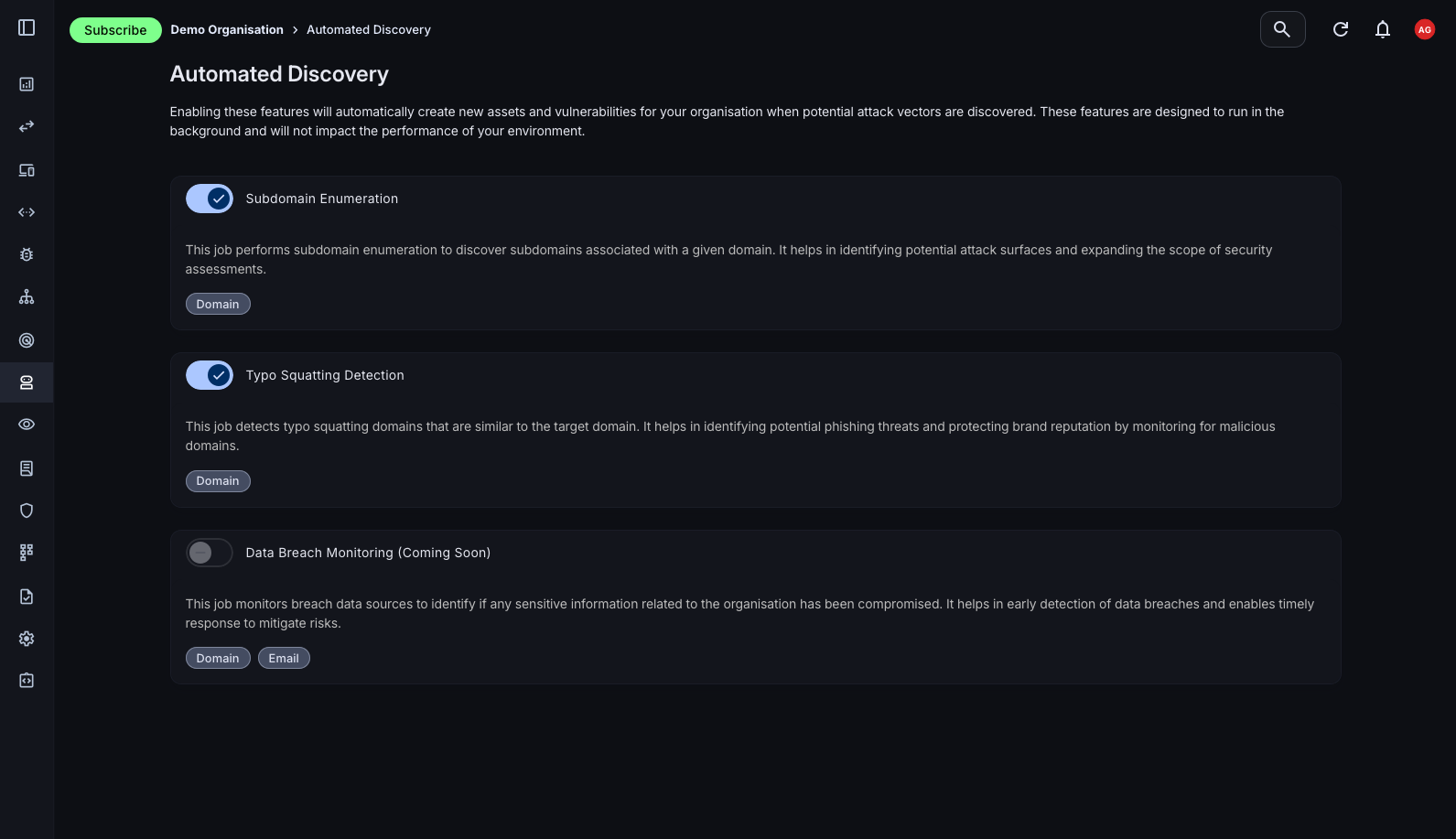
Automated asset discovery
Passive reconnaissance continuously surfaces subdomains, IP addresses, and cloud resources associated with your domains - without sending traffic to your infrastructure.
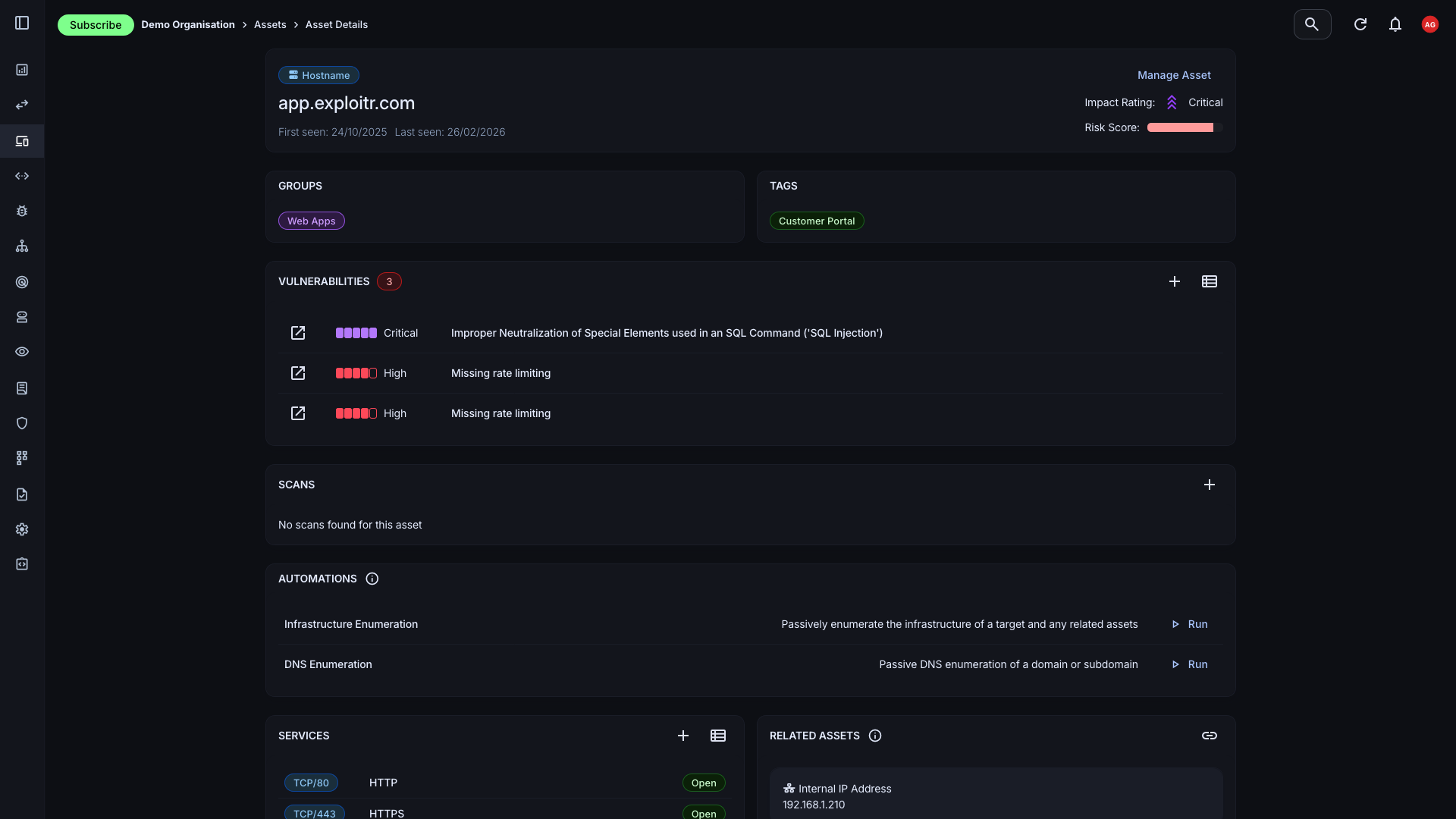
Service and port visibility
Scanning surfaces exactly which ports are open and which services are running on each asset, updated with every scan cycle.
Shadow IT detection
Subdomains and resources created outside your normal IT processes are surfaced automatically, giving you visibility of assets you didn't know existed.
Cloud and on-premises coverage
Pull assets from AWS, Cloudflare, and GitHub alongside on-premises systems. All inventoried and managed in one place.
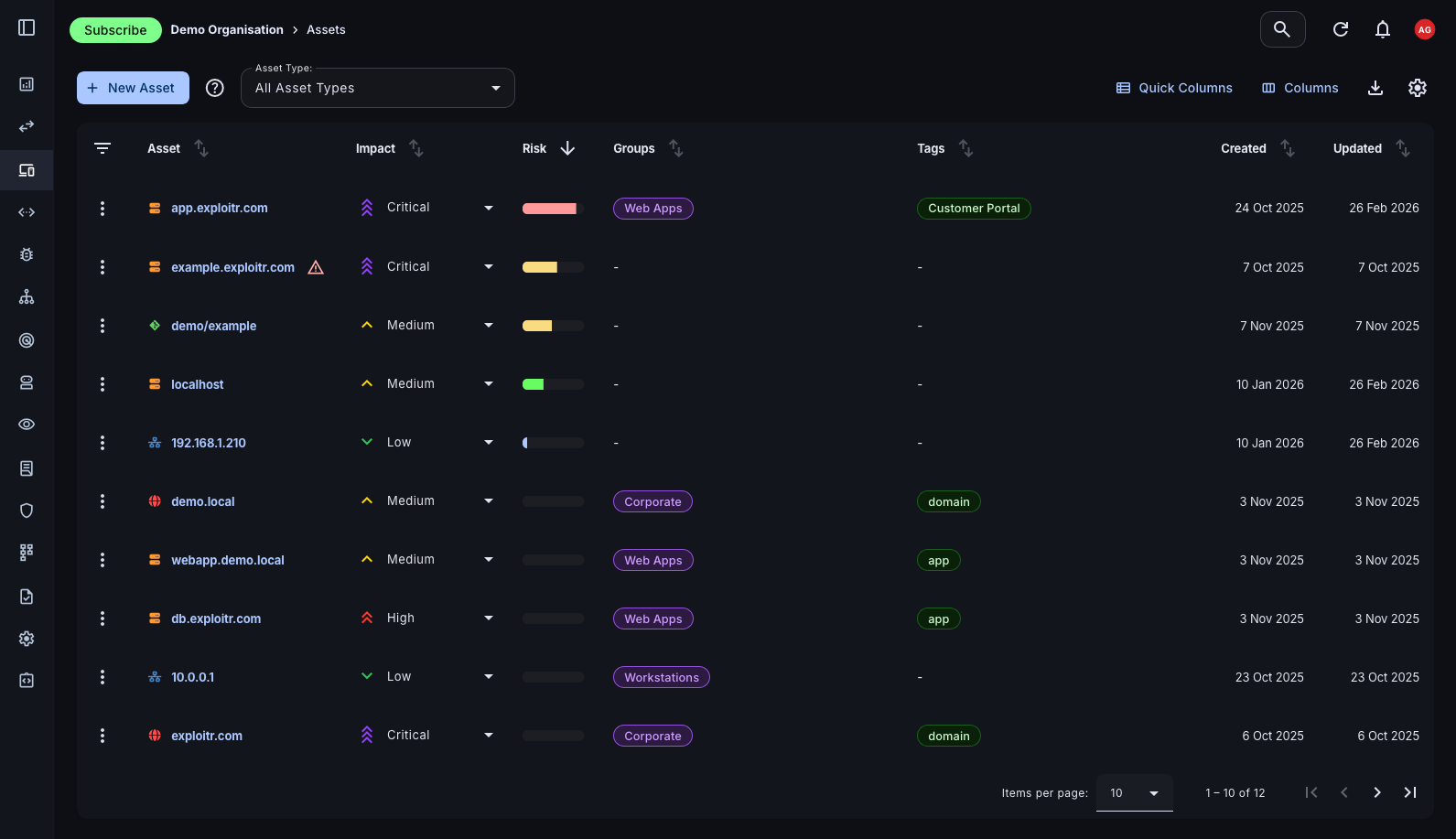
A living inventory that keeps itself current
A static asset register is out of date within days. The Attack Surface Center maintains your inventory automatically through scheduled discovery, integration polling, and scan results - so the picture you're working from reflects the real state of your environment.
- Multiple asset types: Hostnames, domains, IP addresses, cloud resources, applications, and email addresses - the full breadth of your external attack surface represented in one inventory.
- Group organisation: Organise assets into groups by environment, team, or business function to filter, report, and prioritise by context.
- Rich asset context: Each asset record carries its risk score, associated vulnerabilities, discovered services, DNS records, and WHOIS data - all automatically enriched.
Surface assets you didn't know were exposed
Old development subdomains, forgotten cloud instances, and infrastructure created by contractors are among the most common sources of serious breaches. Automated discovery uses passive intelligence sources to map your external footprint without requiring any manual effort or active probing.
- Subdomain enumeration: Curated wordlists and certificate transparency log monitoring surface subdomains associated with your root domains, including those you've lost track of.
- Certificate transparency monitoring: New TLS certificates are often the earliest signal of a new deployment. CT log analysis surfaces these the moment they're issued.
- IP and email discovery: Discover IP addresses and email addresses associated with your domains through passive DNS resolution, WHOIS, and OSINT sources.
- Email security posture: Automatically check for the presence of SPF, DKIM, and DMARC records to identify gaps in your email security configuration.
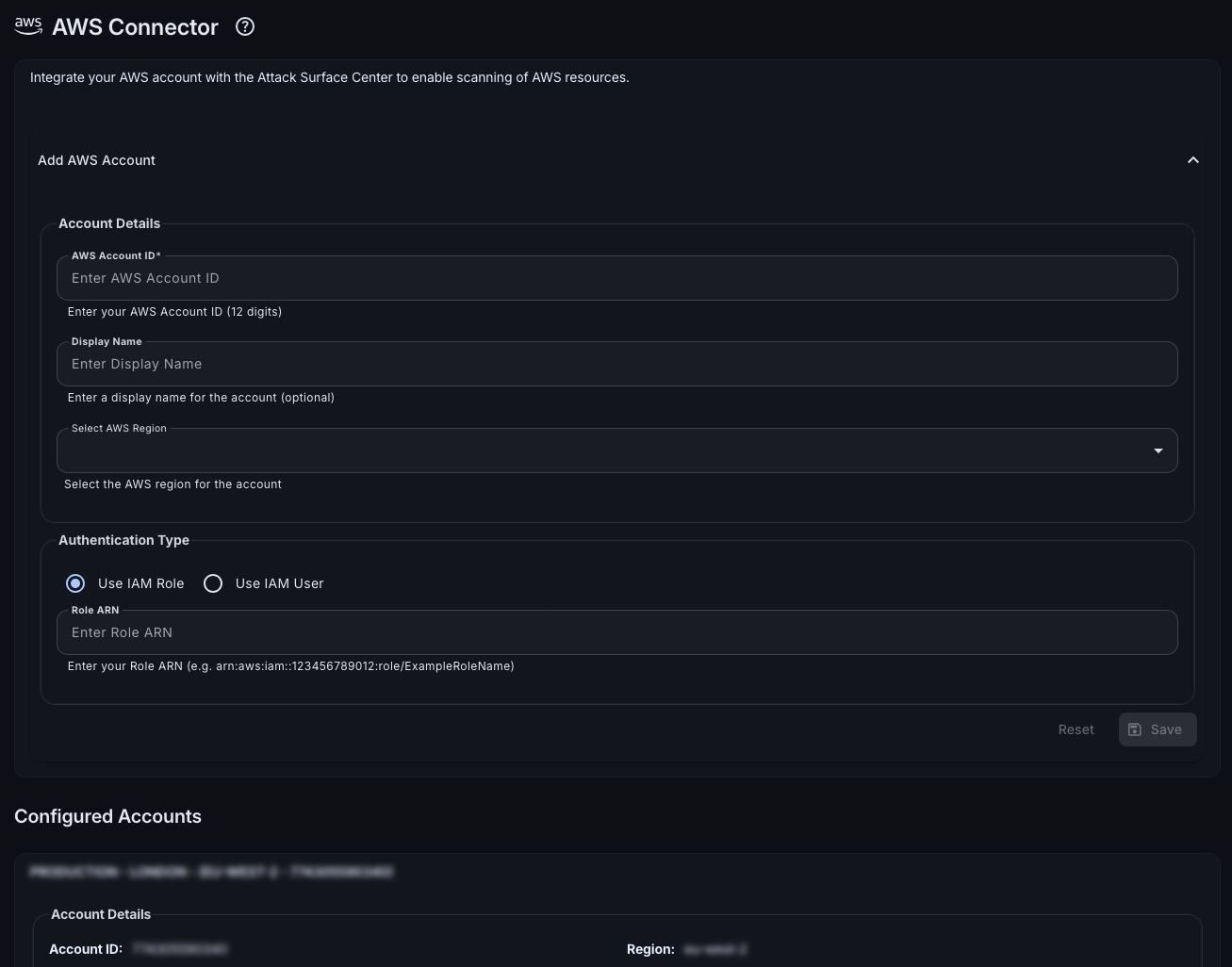
Connect the tools your infrastructure team already uses
Asset data shouldn't live only in Attack Surface Center. Pull your existing infrastructure inventory directly from the platforms where it lives, consolidating everything into a single managed view without manual entry.
- AWS: Import EC2 instances, S3 buckets, and other AWS resources directly into your asset inventory and keep them synchronised automatically.
- Cloudflare: Pull DNS zones and records from Cloudflare to surface all externally exposed hostnames managed through your Cloudflare account.
- GitHub: Import repositories as assets to track the external footprint of your codebase and associated infrastructure.
Get full visibility of your external-facing infrastructure
Sign up free. Automated discovery starts from your first verified domain with no manual configuration required.
Common questions
Automated discovery uses entirely passive techniques: certificate transparency log analysis, DNS enumeration, WHOIS lookups, and curated subdomain wordlists. It draws from public intelligence sources only and never sends traffic directly to your assets, so there is zero operational impact.
Yes. The platform integrates directly with AWS, Cloudflare, and GitHub to pull asset data. You can also import from CSV or supported vulnerability scanner output formats.
Newly discovered assets are automatically added to your inventory. They appear on the Attack Surface Map and are immediately available for scanning or manual review. You can configure who receives notifications when new assets are discovered.
The platform supports hostnames, domains, IP addresses, URLs, cloud resources (AWS, Azure, GCP), applications, email addresses, code repositories, and user accounts. Essentially any component of your external attack surface can be represented.
Yes. Assets can be organised into groups to reflect your environment segmentation, team structure, or business unit. Filtering, reporting, and access controls can all be scoped by group.