Solutions
Attack Surface Management for Security Operations Teams
Security operations teams need signal, not noise. Attack Surface Center gives you continuous visibility into your external attack surface so you can detect changes, prioritise findings, and drive remediation without switching between tools.

Built around how security operations teams actually work
Security operations doesn’t have time for tools that generate more work than they resolve. Attack Surface Center is designed to surface what matters, connect it to context, and give your team a clear path from detection to closure.
Continuous asset monitoring
Automated discovery runs in the background to surface new assets, subdomains, and external threats as they appear - not just when you remember to look.
Prioritised findings
Vulnerabilities are scored by severity, asset risk, and attack chain context, so you know what to act on first without manually triaging everything.
Collaborative remediation
Assign findings to team members, track status, and add commentary - all within the platform. No spreadsheets, no lost context.
Consolidated tooling
Asset management, vulnerability tracking, scanning, risk management, and reporting in one place. Less context-switching, more time on work that matters.
From detection to closure in one platform
Attack Surface Center supports your entire security operations workflow, from discovering unknown assets to closing resolved findings.
Discover
Passive reconnaissance continuously surfaces assets, subdomains, and threats across your external attack surface.
Inventory
Every asset is automatically catalogued, enriched with DNS, WHOIS, and service data, and reflected on the Attack Surface Map.
Scan
Port and web application scans probe your inventory for exposed services and vulnerabilities on demand or on a schedule.
Prioritise
Risk scores, severity ratings, and attack chain context help your team focus on what poses the greatest threat.
Remediate
Assign tasks, track progress, and close findings - with full audit trail and team collaboration built in.
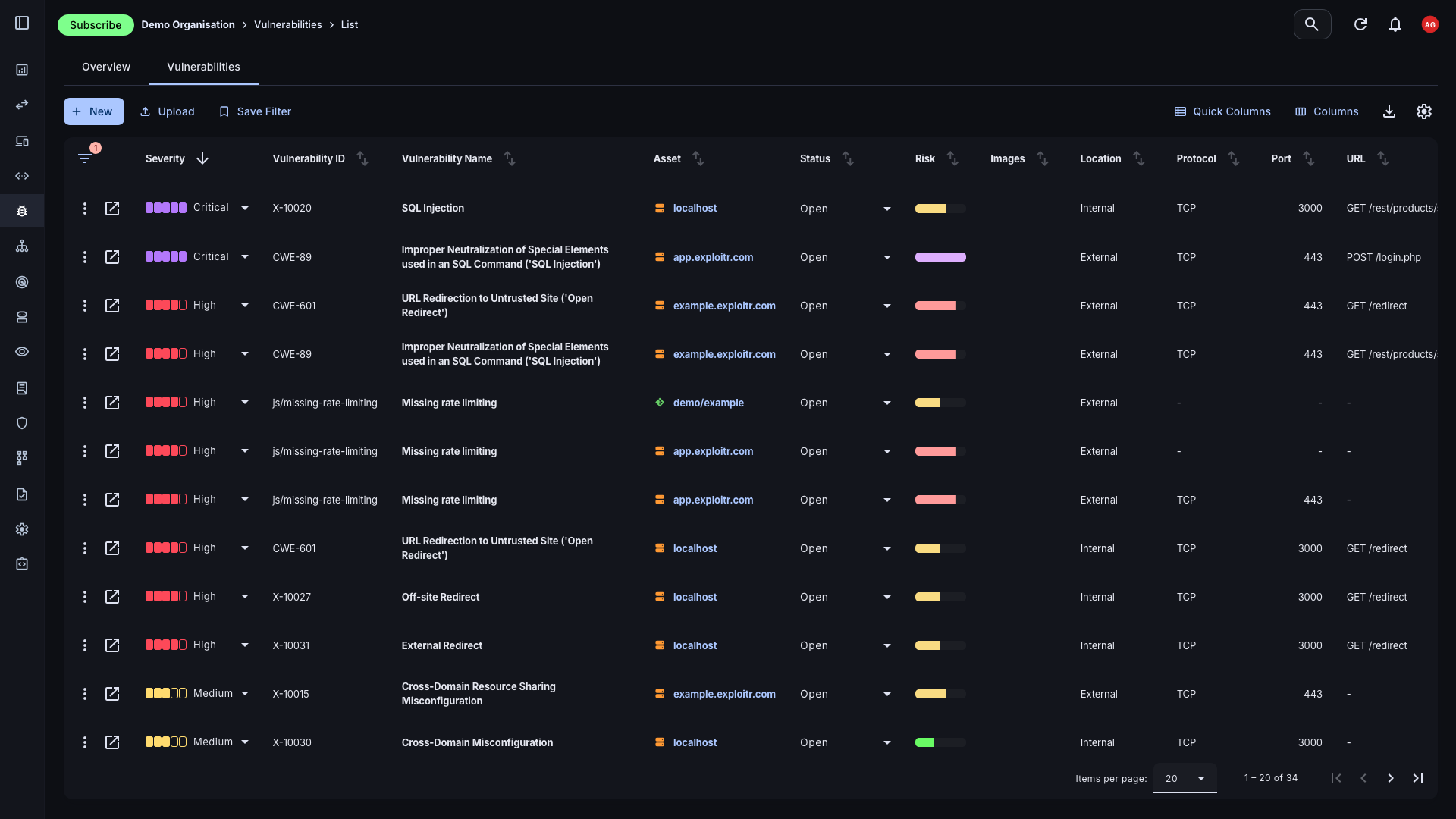
Triage and track every finding
The vulnerability list gives you a filterable, sortable view of every finding across your environment. Filter by severity, status, asset, or source, and drill into individual records for the context you need to act quickly and accurately.
- Source tracking: Know exactly where each finding came from - automated scan, manual import, penetration test report, or integration - so your team has full context from the outset.
- Status and ownership: Set status, assign ownership, and add commentary to each finding to keep remediation on track across the team.
- Risk scoring: Every vulnerability carries a normalised risk score combining severity, impact, and asset context to help you prioritise consistently.
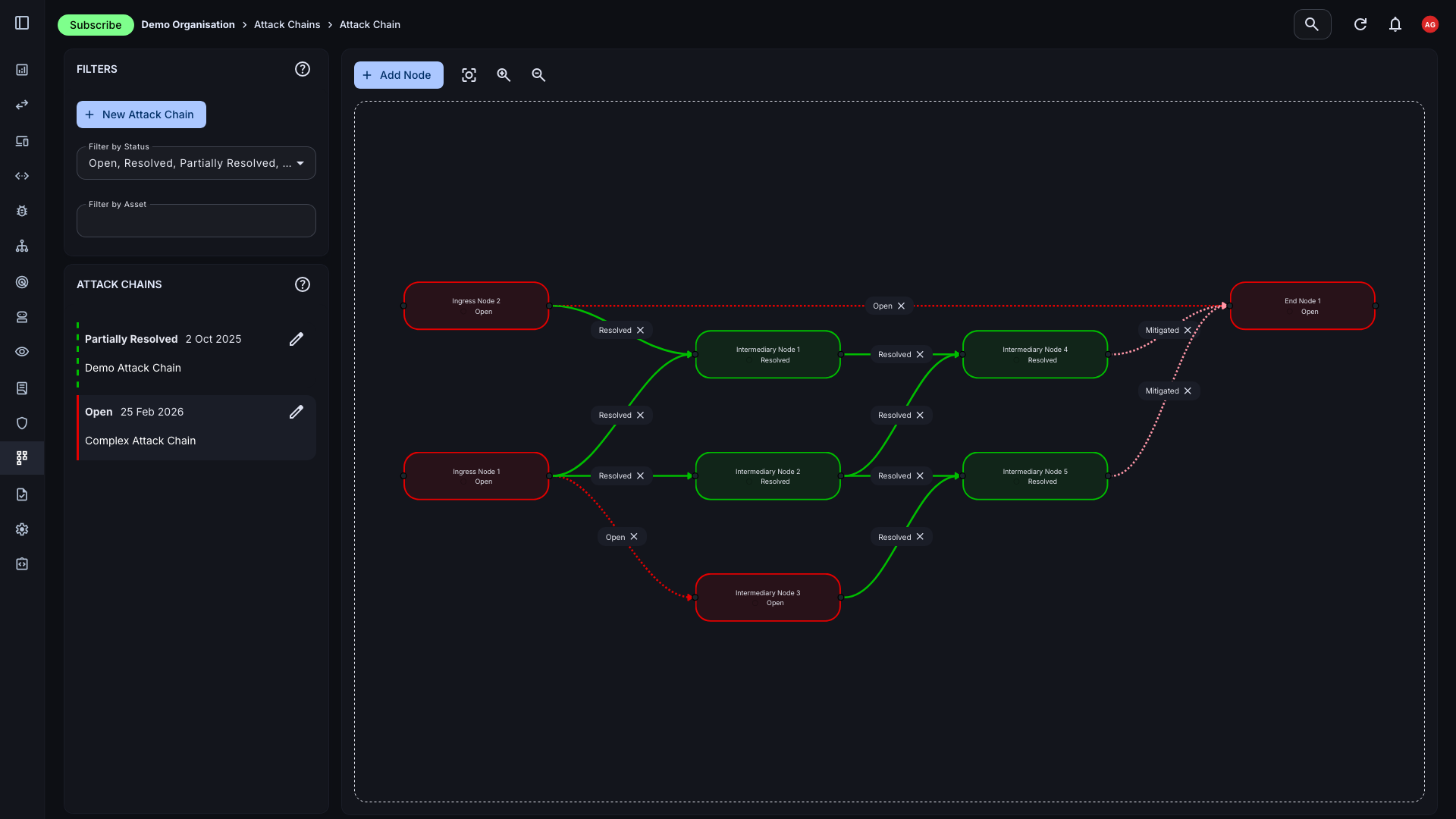
Understand how vulnerabilities connect
Individual vulnerabilities rarely tell the full story. The attack chain view lets you map relationships between findings and assets to identify the minimal viable path an attacker could exploit - and close it before they do.
- Relationship mapping: Visualise how vulnerabilities relate across assets, services, and your broader environment to understand lateral movement risk.
- Minimal remediation paths: Identify the smallest set of fixes that breaks the most attack chains, so your team can maximise impact with limited time.
- Contextual prioritisation: Chain-connected vulnerabilities are surfaced as higher priority, reflecting their actual risk rather than their standalone CVSS score.
Everything your security operations team needs
The tools to discover, monitor, assess, and remediate - without the complexity of managing a stack of disconnected products.
Asset Management
A living inventory of your external assets, updated automatically through discovery, integrations, and scans.
Learn moreVulnerability Scanning
Port and web app scans that feed findings directly into your vulnerability management workflow.
Learn moreAutomated Discovery
Passive, continuous reconnaissance across your external attack surface - subdomains, IPs, threats, and more.
Learn moreAttack Chain Mapping
Visualise relationships between vulnerabilities and identify the highest-leverage remediation opportunities.
Learn moreIntegrations
Connect Slack for alerts, AWS and Cloudflare for asset data, and GitHub for repository visibility.
Learn moreTask Management
Turn findings into tracked tasks with owners, deadlines, and status - built into the same platform.
Learn moreGive your security operations team real visibility
Sign up free. No credit card required. Get your first assets discovered and your first scan running in minutes.
Common questions
You can sign up, verify your first domain, and have automated discovery running within minutes. First scan results typically appear within a few minutes of launching a scan. There is no lengthy onboarding or professional services engagement required.
It can, but it doesn’t have to. You can import results from existing tools such as Nmap and OWASP ZAP into the platform alongside native scan results. This lets you centralise management without immediately replacing your existing tooling.
Automated discovery uses entirely passive techniques - certificate transparency logs, DNS intelligence, OSINT, and curated wordlists - and never sends traffic to your assets. Active scanning probes your assets directly to identify open ports and services. Both are available in the platform and serve complementary purposes.
Yes. The platform integrates with Slack to push notifications when new findings are identified. Additional integration options are on the roadmap.
Each vulnerability receives a normalised risk score based on its CVSS severity, the risk context of the associated asset, and whether it appears in attack chain paths. This gives your team a consistent, data-driven basis for prioritisation rather than relying purely on raw CVSS scores.