See Your Attack Surface the Way an Attacker Does
Most asset inventories show you a list. The Attack Surface Center shows you a map.
See your entire attack surface as an interactive map. Risk highlighted nodes, attacker-path topology, and plain-language priorities – so you know exactly where to focus first.
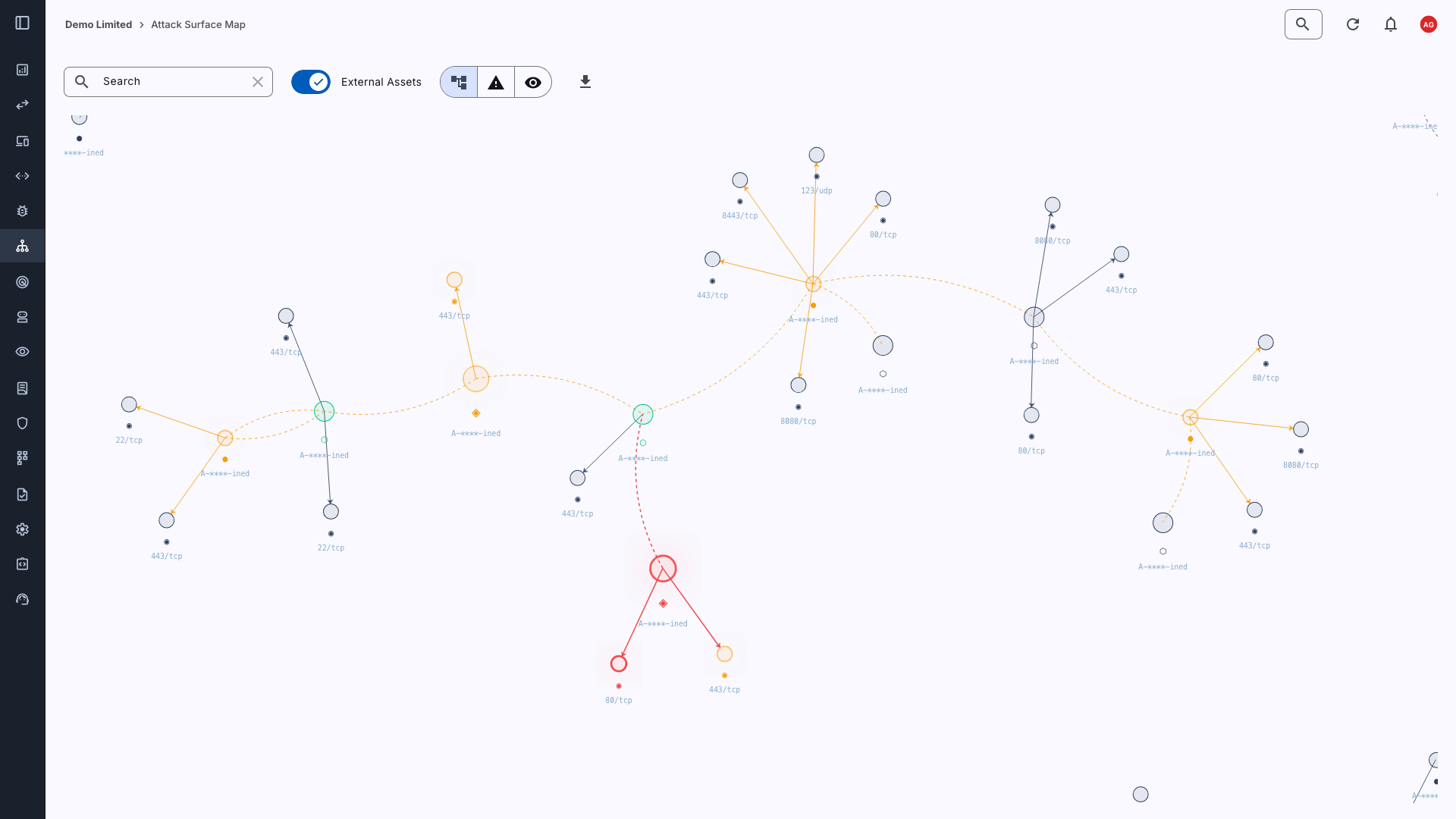
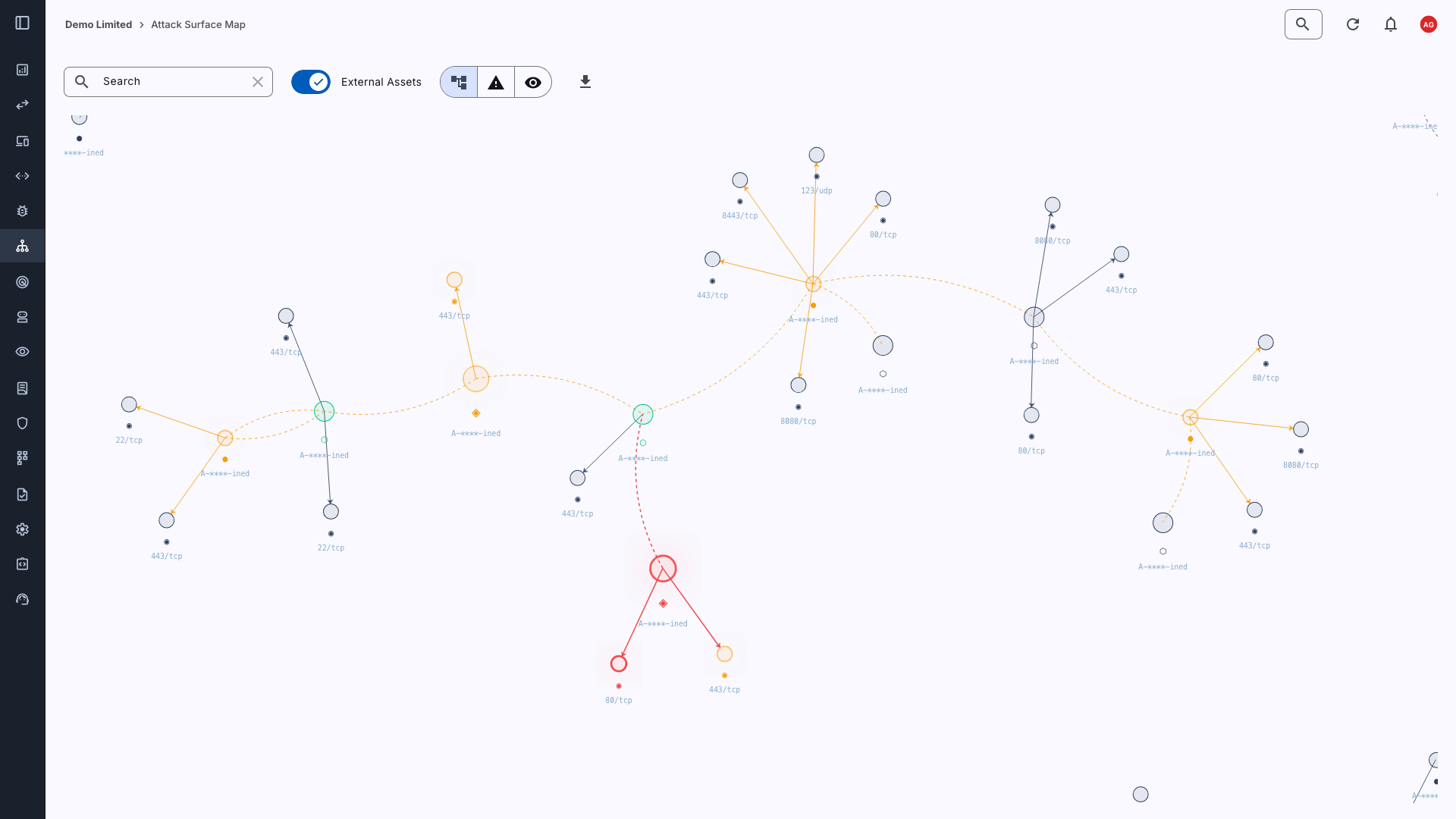
Topology That Mirrors Real-World Exposure
Your attack surface isn’t a list of assets grouped by type. It’s a chain of reachable things: a domain that resolves to an IP, an IP that exposes a service, a service that connects to infrastructure you thought was internal. The Attack Surface Map is built around that reality.
Entry points anchor the graph. Internet-facing domains and public IPs sit at the top, with everything reachable from them – IP addresses, open ports, services, code repositories, email addresses. Relationships are drawn from authoritative sources where possible: direct integrations with AWS, Cloudflare, and other providers confirm what’s connected to what, rather than relying on inference alone.
Risks you can see without searching
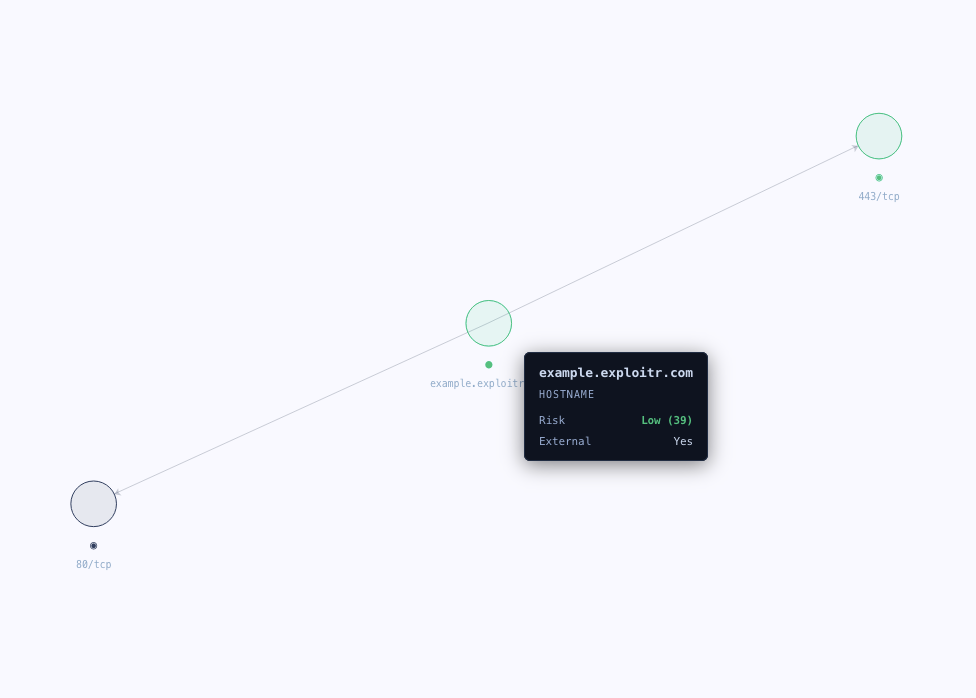
Nodes are coloured by risk score. Critical and confirmed-compromised assets glow. The edges between them carry the risk of the path, so a chain from a public domain through an unauthenticated port to an internal service lights up end-to-end, not just at the vulnerable node.
Three views let you cut through noise instantly:
- Risk view: zero-risk assets step back, leaving only what needs attention visible
- Exposed view: collapse to only high and critical risk assets and their immediate relationships
- Full view: the complete picture when you need to understand broader context
The map is the evidence – not the interface you have to interpret yourself.
Relationships Built From Sources You Can Trust
A relationship that comes from our Cloudflare DNS integration is more reliable than one inferred from a scanner seeing an IP respond to a hostname. The Attack Surface Center tracks where every relationship came from.
Direct integrations with cloud and DNS providers populate high-confidence connections automatically. Scanner-discovered relationships are captured separately. As you add enable these integrations the map fills in with verified topology rather than guesswork.
CDN and proxy infrastructure is handled intelligently. Where an IP is known shared infrastructure, the map avoids creating false connections between unrelated assets behind the same edge provider.
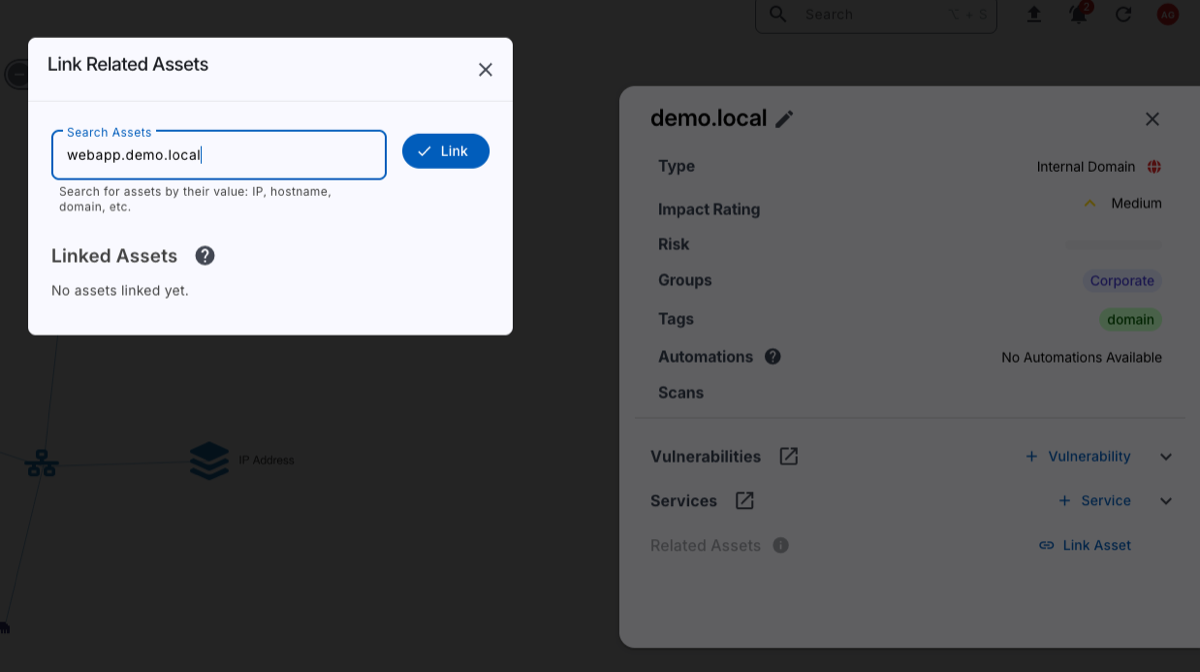
Explore, Search, and Share
Understand the landscape of your organisation’s assets and infrastructure through the interactive attack surface map.
- Search for any asset by name and the graph focuses on it and its immediate neighbours
- Zoom-aware labels keep the view readable at any scale, and detail appears as you zoom in
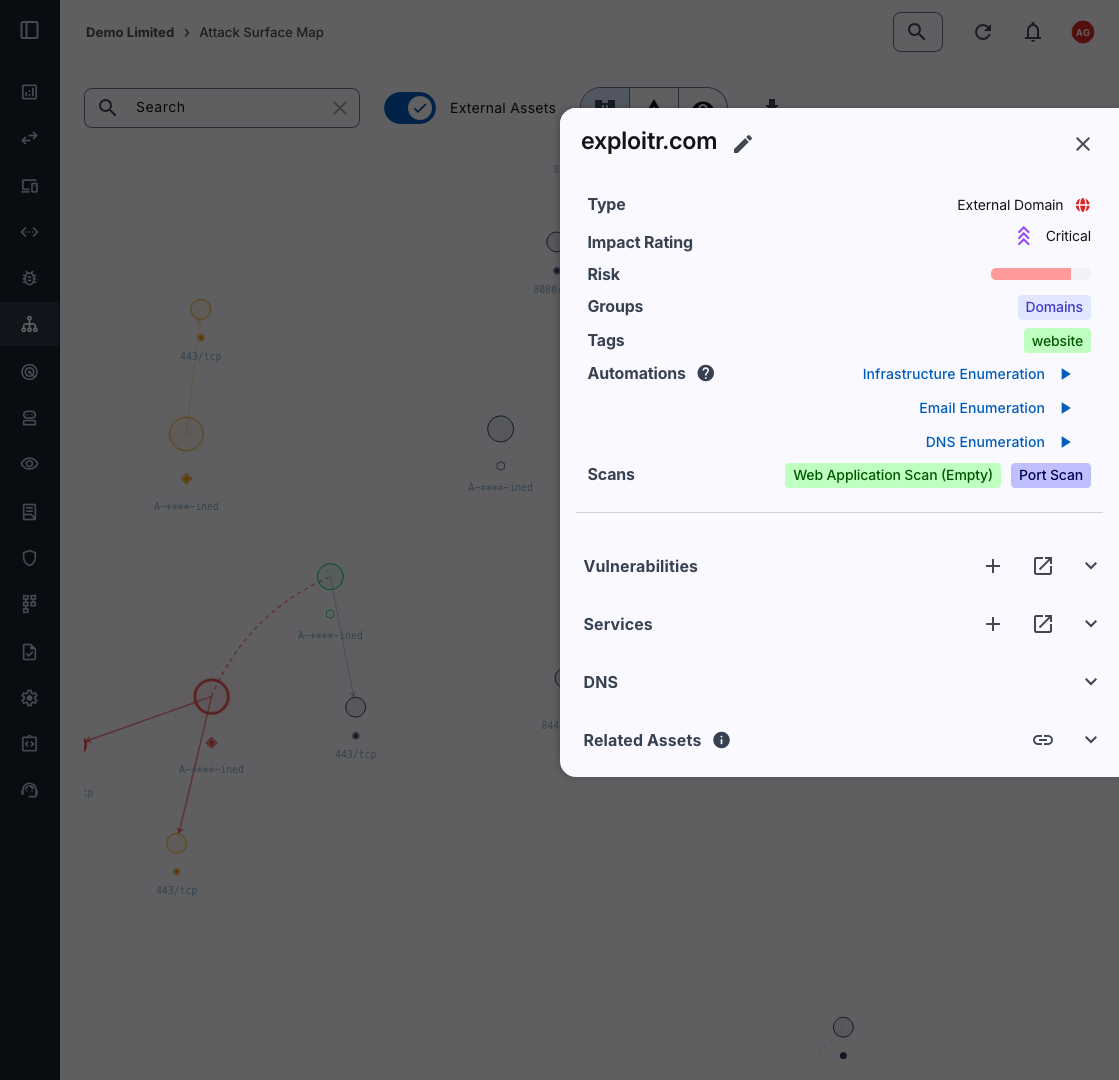
- Click any node to view the asset details, risk findings, and service breakdown in a side panel
- Export the map as an SVG for reports or stakeholder briefings
- Share a focused view with a direct URL – useful for handing off remediation context to a specific team
Always Current
The map updates automatically as your scanners run, integrations sync, and assets are added or removed.
You’re not looking at a point-in-time snapshot – you’re looking at your attack surface as it stands right now.
Get Started with Attack Surface Mapping
Sign up to the Attack Surface Center today and experience the benefits of customisable penetration testing reports, asset management, and vulnerability management.
An Attack Surface Map is an interactive graph that shows your organisation’s internet-facing infrastructure organised around how an attacker would traverse it – from entry points like domains and public IPs, through to the services, repositories, and internal assets reachable from them.
Unlike a flat asset list, a map shows you relationships and exposure paths, making it possible to understand not just what you have, but how it’s connected and what risk flows through those connections.
An asset inventory tells you what exists. An attack surface map tells you what’s reachable, what’s connected to what, and where risk propagates.
The Attack Surface Center’s map is organised around attacker-path topology rather than asset categories, so the structure of the graph itself reflects real-world exposure rather than an internal classification system.
Relationships are populated from multiple sources with different confidence levels. Direct integrations with providers like AWS and Cloudflare supply authoritative, confirmed connections. Active scanning fills in additional topology.
As you connect more integrations, the map becomes more complete and more accurate, with shared or CDN infrastructure handled separately to avoid false connections between unrelated assets.
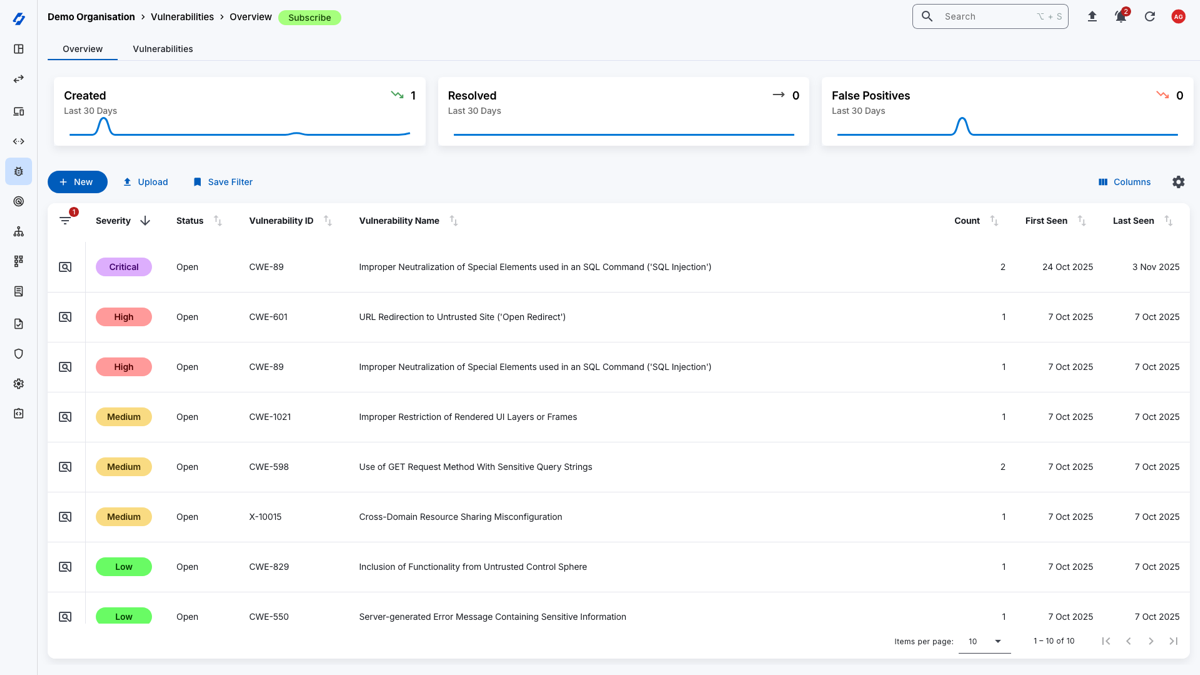
The Attack Surface Map can help your organisation improve its security posture by providing a clear overview of your cyber attack surface. By visualising the assets, vulnerabilities, and services, you can identify potential attack paths and key areas of risk.
This allows you to prioritise remediation efforts effectively, ensuring that you focus on the most critical issues first.
Additionally, the interactive nature of the map enables you to explore your attack surface in real-time, making it easier to stay informed about your security posture as your environment evolves.
See what the Attack Surface Center can do for you
The Attack Surface Center is a powerful Attack Surface Management (ASM) platform that helps you discover, manage, and secure your attack surface.
With features like asset discovery, risk management, and vulnerability scanning, the Attack Surface Center provides you with the tools you need to protect your organisation from cyber threats.