Automated Asset Discovery Without Active Scanning
Discover your external attack surface through passive reconnaissance and intelligence-led enumeration.
Automated discovery runs unseen in the background to regularly identify assets and potential weaknesses within your attack surface.
Discover Assets Unknown to You
Attack Surface Center’s automated discovery capabilities passively identify your organisation’s assets across your external attack surface without sending traffic to your infrastructure. Our automated reconnaissance discovers subdomains, IP addresses, web applications, and forgotten infrastructure that could expose your organisation to cyber threats.
Unlike active vulnerability scanning, which sends traffic to your systems, the automated discovery tools use passive techniques that include certificate transparency log analysis, DNS intelligence, OSINT data sources, and curated subdomain wordlists to map your attack surface without touching your infrastructure. This non-invasive approach discovers assets continuously without operational impact, scan notifications, or potential service disruptions.
Automated discovery runs continuously in the background, identifying new assets as they’re exposed and detecting shadow IT resources created outside your normal IT processes. From newly deployed cloud instances to forgotten development subdomains, our passive reconnaissance provides comprehensive visibility into your expanding attack surface.
Discover your complete external attack surface from £99/month.
Sign up to the Attack Surface Center today and experience the benefits of automated vulnerability scanning and management to help map your attack surface.
Subdomain Enumeration and Discovery
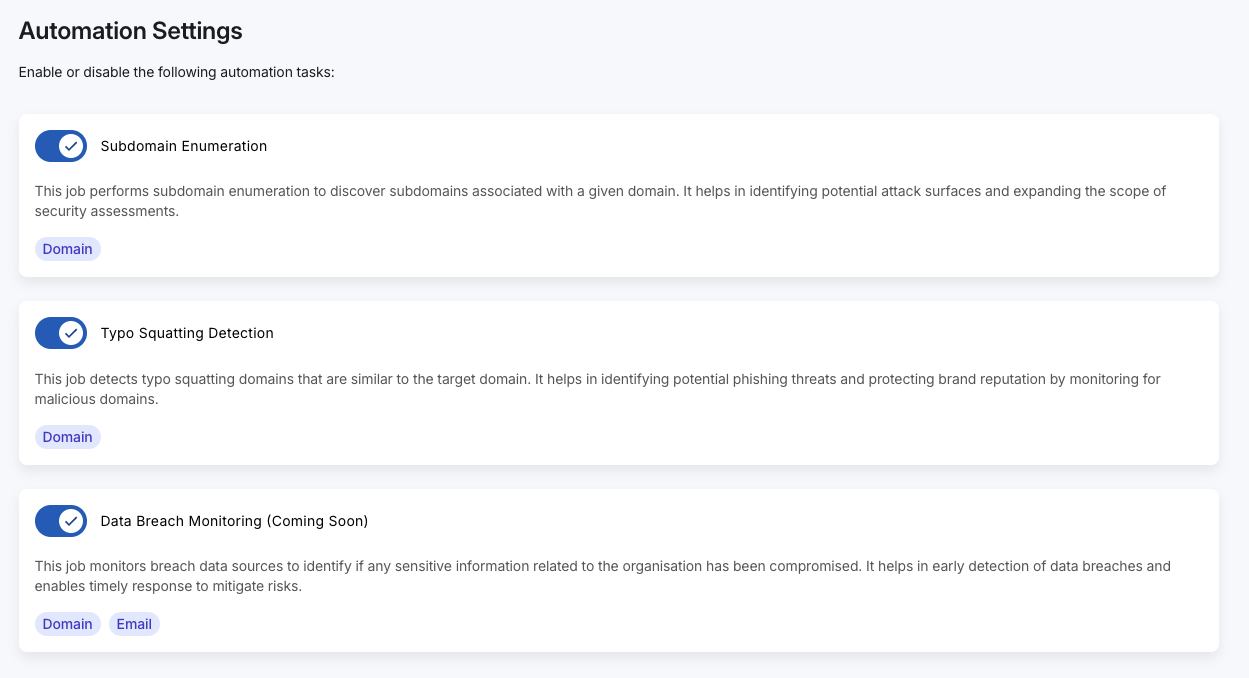
Discover all subdomains associated with your organisation’s domains through automated enumeration that combines multiple intelligence sources. Our passive subdomain discovery identifies active and historical subdomains without sending any traffic to your DNS servers, web applications, or infrastructure.
Subdomain Discovery Techniques
Certificate Transparency Logs: Public certificate transparency (CT) logs contain records of all SSL/TLS certificates issued for your domains. We continuously monitor CT logs to discover new subdomains the moment certificates are issued, providing near-real-time visibility into newly deployed assets.
DNS Intelligence: Aggregate DNS data from passive DNS databases, DNS intelligence platforms, and historical DNS records identifies subdomains from past DNS queries and resolutions.
Curated Wordlist Enumeration: Intelligence-led subdomain wordlists containing common subdomain patterns (www, mail, vpn, dev, staging, admin, etc.) combined with your organisation-specific naming conventions discovers likely subdomains.
OSINT Data Sources: Open-source intelligence from search engines, web crawls, GitHub repositories, and other public sources reveals subdomains referenced in code, documentation, or web content.
Automated Discovery Integration: Discovered subdomains automatically populate your asset management inventory and your interactive attack surface map, providing immediate visibility without manual data entry.
Continuous Monitoring: Subdomain discovery runs continuously, identifying new subdomains as they’re deployed. Receive alerts when new attack surface emerges.
Detect Typosquatting and Phishing Domains Targeting Your Brand
Attackers register domain names similar to your legitimate domains to conduct phishing attacks, distribute malware, or damage your brand reputation. These typosquatting domains exploit common typing mistakes, character substitutions, and similar-looking domain names to deceive users into believing they’re interacting with your organisation. Our tools have you covered.
Typosquatting Detection Capabilities
Homoglyph Detection: Identify domains using visually similar characters from different alphabets (e.g., replacing ‘a’ with Cyrillic ‘а’, ‘o’ with ‘0’). These international domain name (IDN) homoglyph attacks are difficult for users to spot but easy for automated systems to detect.
Character Substitution: Discover domains with common character substitutions (e.g., ‘attacksurfacecenter’ → ‘attacksurfacecentre’, ‘attaксurfacecenter’)
Hyphenated Variants: Find domains inserting hyphens into your domain name (e.g., ‘attack-surface-center.com’) that users might accidentally visit or attackers use for phishing.
Common Typos: Identify registered domains exploiting common typing mistakes and character transpositions based on keyboard layout and typing patterns.
Subdomain Typosquatting: Detect malicious actors creating subdomains on compromised domains designed to impersonate your legitimate subdomains.
Brand Monitoring: Continuous monitoring discovers newly registered typosquatting domains within days of registration, enabling you to enact rapid takedown actions before significant phishing activity occurs.
Receive alerts when potentially malicious domains are discovered, investigate the threat level, and coordinate takedown efforts with domain registrars or legal teams.
How Automated Discovery Works
Attack Surface Center’s automated discovery operates entirely through passive reconnaissance, gathering intelligence about your attack surface without sending any traffic to your infrastructure.
Discovery Process
Domain Verification: After you verify domain ownership, our automated discovery tools begin continuous monitoring. Verification ensures we only discover assets you’re authorised to enumerate.
Continuous Intelligence Gathering: Our systems continuously monitor certificate transparency logs, passive DNS databases, OSINT sources, and other intelligence feeds for information about your domains.
Asset Identification: Discovered subdomains, IP addresses, and infrastructure are automatically validated, classified, and enriched with contextual information about hosting providers, technologies, and security posture.
Asset Inventory Population: Valid assets automatically populate your asset management system with details including DNS records, IP addresses, hosting provider, identified technologies, and last discovery date.
Attack Surface Map Updates: Your interactive attack surface map updates automatically as new assets are discovered, providing visual representation of your expanding infrastructure.
No Infrastructure Impact: Automated discovery never sends traffic to your assets, eliminating concerns about scan-induced outages, rate limiting, security control triggers, or operational disruptions.
Discovery speed depends on the asset type and intelligence source. Certificate transparency monitoring discovers new subdomains within minutes of certificate issuance. DNS changes are typically discovered within hours as passive DNS systems observe the changes.
Some assets may take days to discover if they’re not widely accessed or don’t have SSL certificates. Most new production infrastructure is discovered within hours because modern deployments almost always include SSL certificates recorded in CT logs.
Yes – users with permission to manage automations have the ability to toggle the tools at any time.
No, the automated discovery tools will not interact with your resources, so there won’t be any traffic directed at your assets. If, in future, any additional tools are added to the Attack Surface Center that will directly interact with your assets these will be optional features that you can enable manually.
Attack Surface Center’s automated discovery focuses on external attack surface – these are the assets that are accessible from the internet, or are discoverable through public intelligence sources.
Internal infrastructure generally won’t be discovered through passive techniques. However, discovery often identifies internal systems accidentally exposed (development databases with public IPs, misconfigured cloud storage, etc.).
Yes – our team are busy working to integrate new features and toolsets to help you discover not only your external attack surface, but also your internal attack surface.
Sign up to the Attack Surface Center today for free and keep updated on our future releases!
Identify assets and potential threats without lifting a finger.
Attack Surface Center’s automated discovery provides continuous, passive visibility into your external attack surface without operational impact. From subdomain enumeration through typosquatting detection, our intelligence-led reconnaissance discovers the assets attackers will find.