Automated Vulnerability Scanning for Continuous Security Monitoring
Schedule Network Scans and Web Application Security Testing
Our platform provides an integrated solution for asset discovery, port scanning, and vulnerability scanning, allowing you to keep an eye on your attack surface.
Attack Surface Center’s automated vulnerability scanning capabilities enable security teams to continuously monitor their infrastructure for security weaknesses, misconfigurations, and exposed services. Our integrated vulnerability scanning tools combine network port scanning and web application security testing to provide comprehensive coverage across your entire attack surface.
Schedule automated security scans to run continuously at intervals that match your security requirements – weekly, monthly, or annually. Discover open ports and exposed services on your network infrastructure, identify known vulnerabilities in web applications and websites, and maintain real-time visibility into your security posture without manual intervention.
Our vulnerability scanning engine integrates seamlessly with Attack Surface Center’s asset inventory and vulnerability management capabilities. Scan results automatically create or update vulnerability records in your centralised vulnerability management dashboard, enabling efficient prioritisation and remediation workflows.
Get Started with Vulnerability Scanning
Sign up to the Attack Surface Center today and experience the benefits of automated vulnerability scanning and management to help map your attack surface.
Network Port Scanning
Discover exposed network services and potential attack vectors with Attack Surface Center’s automated network port scanning capabilities. Our port scanner identifies open ports across your infrastructure, revealing which services are accessible to attackers and helping you understand your network exposure.
Network Port Scanning Features
Flexible Scanning Targets: Scan IP addresses, hostnames, and domains. Configure scans for specific network segments, public-facing infrastructure, or your complete IP inventory.
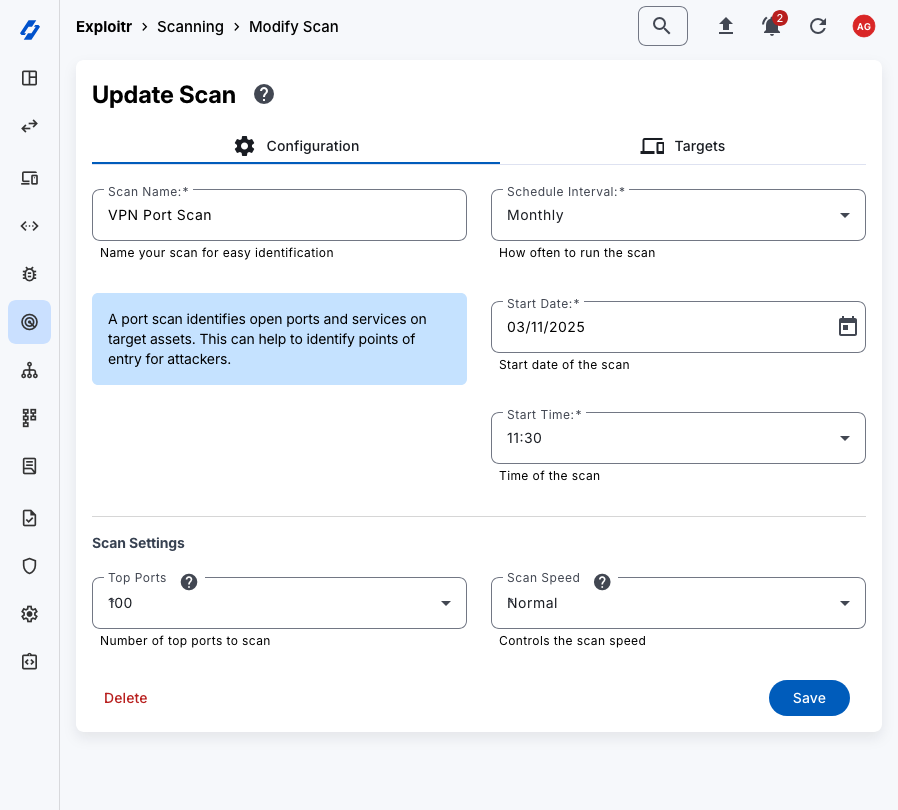
Customisable Port Ranges: Scan the most commonly exposed ports, specific port ranges, or perform comprehensive scans across all TCP/UDP ports. Tailor your scanning scope to balance thoroughness with scan duration.
Service Detection: Identify services running on discovered open ports including web servers, databases, SSH, RDP, and other network services. Understand what’s exposed on each port beyond just the port number.
Scheduled Port Scans: Configure automated port scans to run weekly, monthly, or annually. Maintain continuous visibility into your network exposure as infrastructure changes over time.
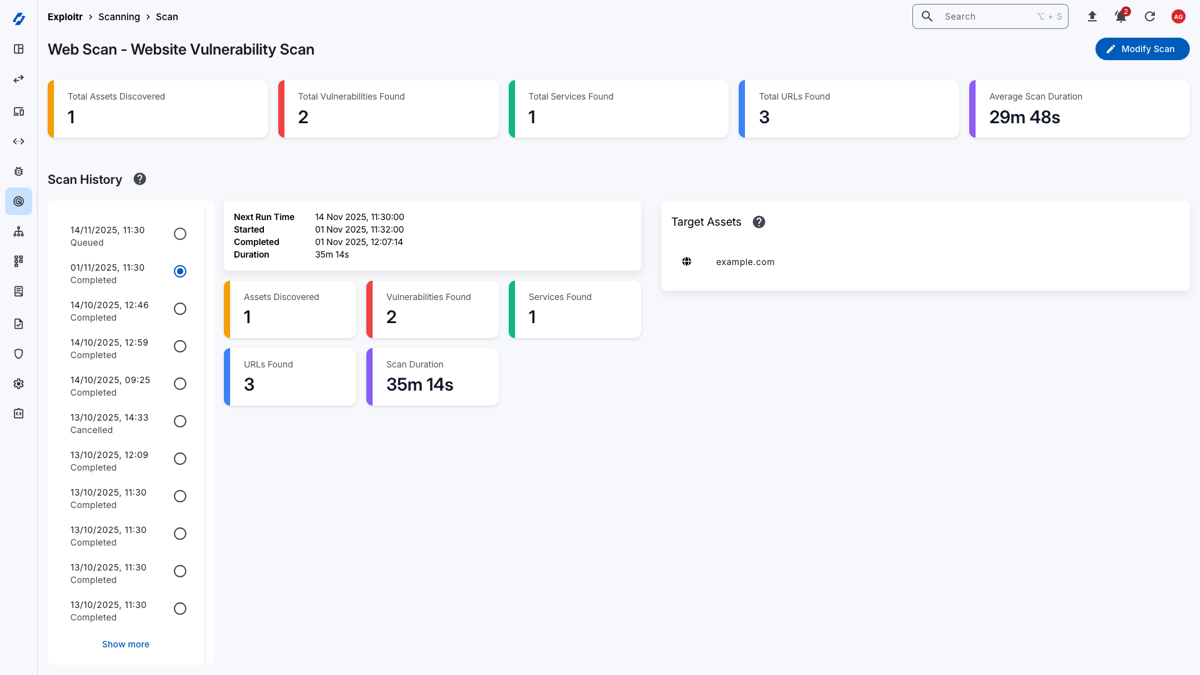
Historical Scan Tracking: View complete port scan history showing how your network exposure evolves. Identify when new ports open or services become exposed, enabling rapid response to unauthorised changes.
Integration with Asset Management: Port scan results automatically update your asset inventory, enriching asset records with discovered services, open ports, and network exposure information.
Web Application Vulnerability Scanning
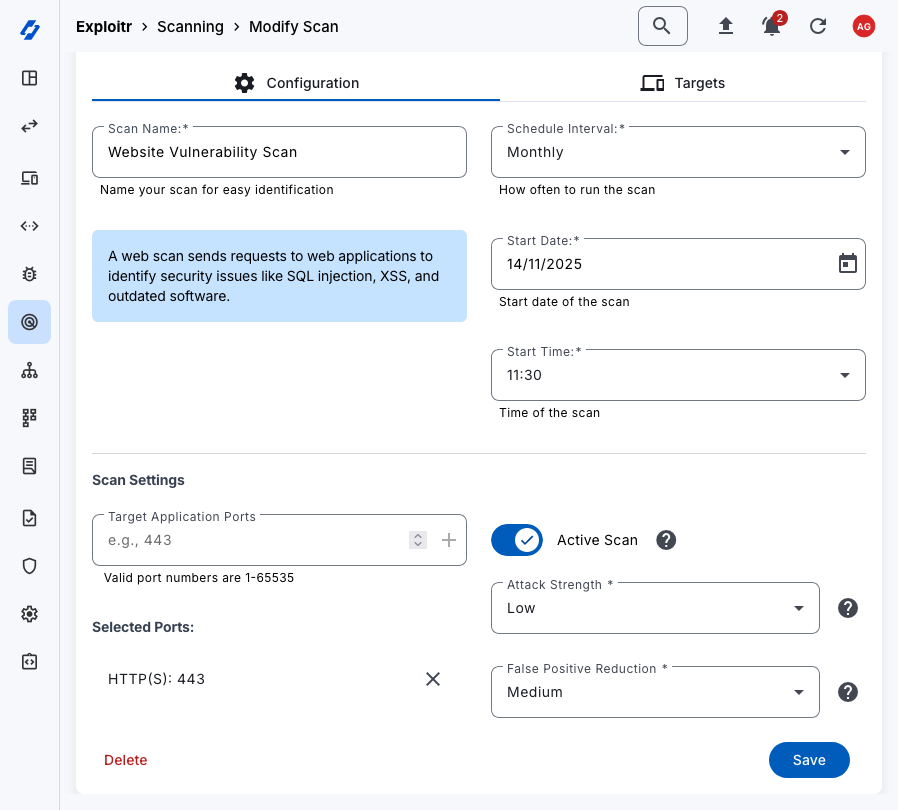
Identify security vulnerabilities in your websites, web applications, and APIs with automated security scanning that tests for common web vulnerabilities and security misconfigurations. Our web application vulnerability scanner continuously monitors your applications for security issues, enabling rapid discovery and remediation of web security vulnerabilities.
Web Application Scanning Capabilities
OWASP Top 10 Coverage: Scan for critical web vulnerabilities including SQL injection, cross-site scripting (XSS), security misconfigurations, sensitive data exposure, and other OWASP Top 10 vulnerabilities.
SSL/TLS Security: Verify SSL/TLS certificate validity, test for weak cipher suites, check for expired certificates, and identify insecure protocol versions.
Security Headers Analysis: Scan for missing or misconfigured security headers including Content Security Policy (CSP), X-Frame-Options, HSTS, and other browser security protections.
Crawling and Discovery: Our scanner automatically crawls web applications to discover pages, forms, and functionality, ensuring coverage across your entire application.
Automations
Utilise our automations to passively discover assets, services, and vulnerabilities in your environment without sending any traffic to your assets. This allows you to gather information about your assets without actively probing them.
Some of our automations include:
- Domain and subdomain discovery
- IP address enumeration
- Email address discovery and enumeration
- DNS enumeration
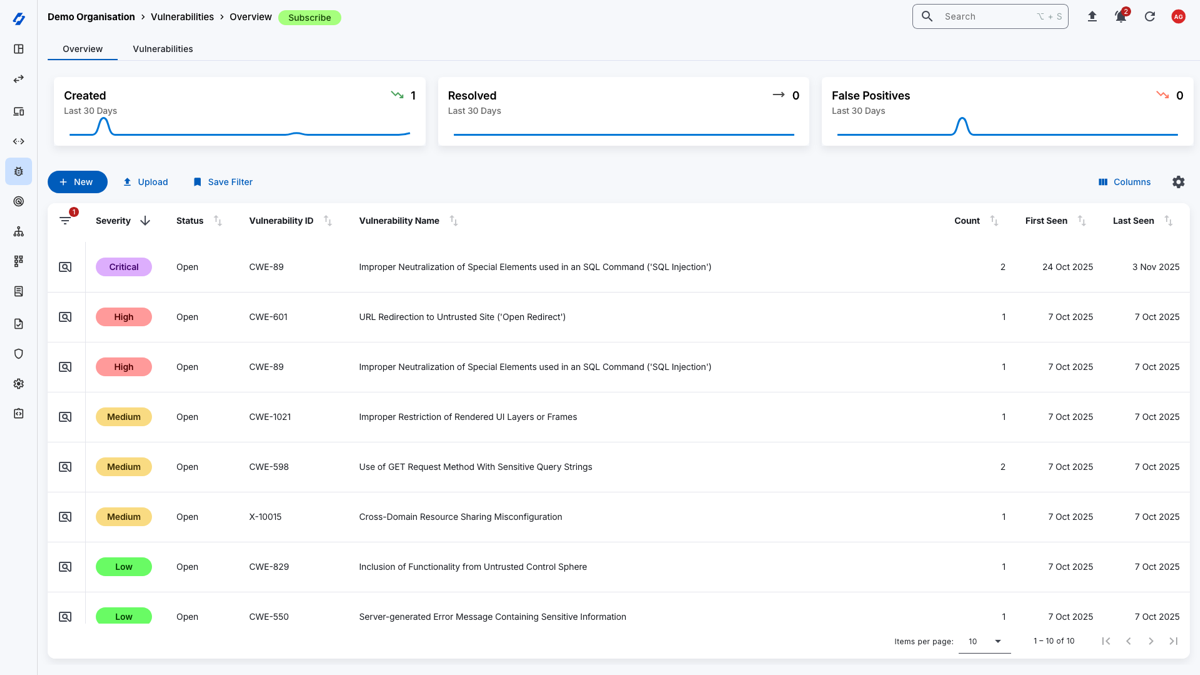
Actionable Vulnerability Scan Results and Discovery
Transform raw vulnerability scan data into actionable security intelligence. Attack Surface Center automatically processes scan results, creates vulnerability records, enriches the findings with contextual information, and prioritises discoveries based on actual risk to your organisation.
Scan Results Management
Automated Vulnerability Creation: Scan results automatically populate your vulnerability management dashboard. New vulnerabilities are created from discovered security issues, while existing vulnerability records are updated with the latest scan findings.
Risk-Based Prioritisation: Scan results are automatically prioritised using our risk scoring algorithm that considers vulnerability severity and affected asset criticality.
False Positive Management: Mark false positives to prevent recurring alerts. Take control into your hands with the full vulnerability management functionality.
Historical Scan Tracking: Access complete scan history for every asset. View how scan results change over time, track remediation progress, and identify trends in your security posture.
Scan Comparison: Compare scan results across different time periods to identify new vulnerabilities, verify successful remediation, or detect security regressions.
Detailed Vulnerability Information: Each discovered vulnerability includes CVE identifiers and CVSS scores (where possible), the affected systems, remediation recommendations, and references to vendor security advisories.
How It Works
Our vulnerability scanning feature is designed to automate the process of identifying and managing vulnerabilities in your environment. Here’s how it works:
- Create Scanning Jobs: You can create port scanning and vulnerability scanning jobs for your assets. This involves selecting the assets you want to scan and configuring the scan settings.
- Schedule Scans: Once you’ve created a scanning job, you can schedule it to run at regular intervals, such as weekly, monthly, or annually. This ensures that your assets are regularly scanned for vulnerabilities and exposed services.
- View Scan Results: After a scan is completed, you can view the results in the Attack Surface Center dashboard. The results will show you any open ports, services, and vulnerabilities that were discovered during the scan.
- Remediate Vulnerabilities: With the scan results in hand, you can prioritise and remediate vulnerabilities based on their severity and impact on your organisation. The Attack Surface Center provides the tools to help you manage and track the remediation process.
- Continuous Monitoring: By scheduling regular scans, you can maintain an up-to-date view of your security posture and quickly address any new vulnerabilities that may arise.
The Attack Surface Center supports various types of vulnerability scans, including network port scanning and web application vulnerability scanning. You can create and manage scanning jobs to discover open ports, services, and known vulnerabilities in your applications and APIs.
Scan frequency depends on asset criticality, compliance requirements, and rate of change. Best practice would be to scan critical infrastructure weekly, standard production systems bi-weekly or monthly, and less critical systems quarterly. Scan immediately after major infrastructure changes or when significant new vulnerabilities are publicly disclosed.
You can schedule vulnerability scans to run at regular intervals that suit your needs by choosing from weekly, monthly, or annual schedules. This flexibility allows you to maintain an up-to-date view of your security posture.
Yes, if you exceed your monthly asset allowance, you can purchase additional assets at any time. This allows you to scale your scanning capabilities as your network grows or as you add new targets to monitor.
Port scanning focuses on discovering open ports and services on your assets, helping you identify potential attack vectors. Vulnerability scanning, on the other hand, involves scanning your applications and APIs for known vulnerabilities, allowing you to address security issues in your software.
Yes, the Attack Surface Center offers automations that allow you to passively discover assets, services, and vulnerabilities in your environment without sending any traffic to your assets. This helps you gather information about your assets without actively probing them.
Vulnerability scanning is automated testing using tools that identify known vulnerabilities, misconfigurations, and security weaknesses. Penetration testing is manual security testing by skilled security professionals who attempt to exploit vulnerabilities to determine actual business impact.
Vulnerability scanning provides broad, continuous coverage identifying potential issues. Penetration testing provides deep analysis of specific systems validating exploitability.
Most organisations use both: automated vulnerability scanning for continuous monitoring and periodic penetration testing for validation and testing of complex security controls. Attack Surface Center provides automated vulnerability scanning and supports custom assessment report generation for organisations that want to produce their own internal pentest reports.
Modern vulnerability scanners, including the Attack Surface Center, are designed to minimise production impact. Our scanning is non-invasive and doesn’t exploit vulnerabilities or attempt to damage systems.
However, any network activity can potentially impact systems through increased resource usage or due to delicate services or application functionality. Minimise the risk of impact by scheduling scans during maintenance windows, using scan throttling for sensitive systems, and configuring scan intensity appropriately.
Test scanning on development environments first before scanning critical production infrastructure. For extremely sensitive systems, consider using our passive automated discovery capabilities that gather information without directly scanning assets.
Scan for vulnerabilities within your assets. Discover and remediate.
The Attack Surface Center is a powerful Attack Surface Management (ASM) platform that helps you discover, manage, and secure your attack surface.
With features like asset discovery, risk management, and vulnerability scanning, the Attack Surface Center provides you with the tools you need to protect your organisation from cyber threats.